Why data security is vital for protecting business assets

Data breaches now cost organizations an average of $4.44 million globally, with recovery often spanning months and causing massive operational disruption. Despite these staggering numbers, many business leaders still underestimate how critical robust data security is for protecting their digital assets and maintaining competitive advantage. Understanding why data security matters and how to strengthen it isn’t just an IT concern anymore, it’s a fundamental business imperative that affects customer trust, revenue stability, and long-term viability. This guide breaks down the real costs of inadequate protection and shows you practical ways to defend your organization’s most valuable assets.
Table of Contents
- Key takeaways
- The true cost of data breaches and their business impact
- Data security’s role in maintaining customer trust and business continuity
- Emerging risks and advanced data-centric security strategies
- Implementing effective data security to protect digital assets
- Protect your business with expert data security solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Breach cost | The global average cost of a data breach is $4.44 million in 2025, including direct expenses and indirect losses from disruption and defection. |
| Operational disruption | Seventy percent of breaches cause major operational disruption, and recovery commonly takes over 100 days. |
| Customer churn impact | Eighty percent of customers churn after a breach, with affected individuals switching to more secure competitors. |
| Prevention pays off | Proactive security measures cost a fraction of breach response and help prevent cascading losses. |
| Security is business imperative | Data security matters beyond IT and is essential to protecting assets, trust, revenue stability, and long term viability. |
The true cost of data breaches and their business impact
When organizations experience data breaches, the financial damage extends far beyond immediate response costs. The global average cost of a data breach is $4.44 million USD in 2025, representing a 9% decrease from the previous year but still constituting a devastating financial blow for most businesses. Healthcare and financial services organizations face even steeper costs, with some breaches approaching $10 million in total impact. These figures include direct expenses like forensic investigations, legal fees, regulatory fines, and notification costs, plus indirect losses from business disruption and customer defection.
Operational disruption compounds the financial damage significantly. Recent data shows that 70% report major operational impact, recovery often taking over 100 days, with lost business costs continuing to escalate year over year. During recovery periods, organizations struggle with system downtime, productivity losses, diverted IT resources, and delayed product launches. The complexity of modern digital environments means that identifying compromised systems, containing threats, and restoring normal operations requires extensive time and specialized expertise.
The breakdown of breach costs reveals why prevention is so much more cost effective than response:
- Detection and escalation expenses average $1.58 million per incident
- Post-breach response activities including forensics and communications cost $1.31 million
- Lost business from customer churn and reputation damage reaches $1.42 million
- Notification expenses for affected parties add another $0.13 million
Revenue impact continues long after technical remediation completes. Organizations experience sustained customer acquisition cost increases as prospects become more skeptical. Existing customers demand enhanced security guarantees and transparency. Competitive disadvantage emerges as rivals highlight their superior security postures. Stock prices for publicly traded companies typically decline following breach announcements, with recovery taking months or years depending on severity and response quality.
“The escalating disruption from data breaches pushes total costs to record highs, with lost business representing the largest and fastest-growing expense category as customers flee to competitors and operations stall during extended recovery periods.”
Business leaders who invest in IT support services guide 2026 approaches gain significant advantages in preventing these cascading costs. Proactive security measures cost a fraction of breach response while delivering continuous protection. The return on investment for comprehensive data security programs becomes obvious when you compare prevention costs against the multi-million dollar breach scenarios that organizations face without adequate defenses.
Data security’s role in maintaining customer trust and business continuity
Customer relationships represent one of your organization’s most valuable assets, and data breaches destroy trust faster than almost any other business failure. Research demonstrates that data breaches lead to 80% customer churn as affected individuals immediately switch to competitors they perceive as more secure. This massive defection rate reflects fundamental changes in consumer expectations around privacy and security. Customers now view data protection as a baseline requirement rather than a premium feature, and they punish organizations that fail to meet this standard by taking their business elsewhere.
The reputational damage from breaches extends well beyond the immediate customer base. News coverage amplifies awareness of security failures, warning potential customers to avoid compromised organizations. Social media discussions spread negative experiences rapidly across networks. Industry analysts downgrade affected companies in their evaluations. Partners and suppliers become hesitant to share data or integrate systems. This reputational cascade can take years to reverse, even with significant investment in brand rehabilitation.
Implementing robust data protection services creates competitive advantages that strengthen customer relationships:
- Transparent security policies demonstrate commitment to protecting customer information
- Regular security audits and certifications provide third-party validation of protection measures
- Prompt breach notifications and remediation show respect for customer rights
- Privacy-by-design approaches minimize data collection and retention risks
Business continuity depends directly on your ability to maintain operations during security incidents. Organizations with mature data security programs experience shorter disruption periods because they’ve prepared incident response procedures, backup systems, and recovery protocols in advance. They can isolate affected systems quickly, restore from clean backups, and resume critical operations while investigating the breach. Companies lacking these preparations face extended outages that multiply financial losses and customer frustration.

Consumer behavior shifts permanently after experiencing data breaches. Affected individuals become significantly more privacy conscious, scrutinizing data protection statement details before engaging with any organization. They adopt protective behaviors like using unique passwords, enabling multi-factor authentication, and monitoring credit reports. They share cautionary tales with friends and family, amplifying the reputational damage. This heightened awareness means that organizations must continuously demonstrate their security commitment through actions, not just marketing claims.
Pro Tip: When security incidents occur, communicate transparently with affected customers immediately rather than delaying notifications. Prompt, honest disclosure with clear remediation steps helps preserve trust and demonstrates your commitment to customer protection, significantly reducing long-term churn compared to organizations that hide or minimize breaches.
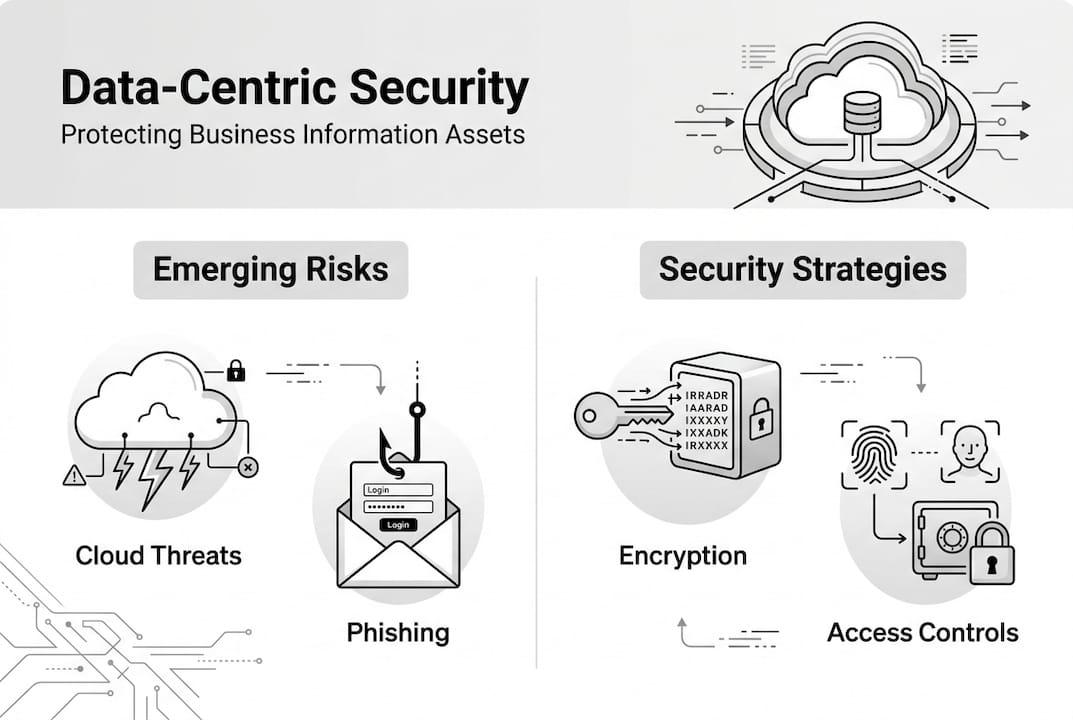
Emerging risks and advanced data-centric security strategies
The security landscape evolves constantly as new technologies create fresh attack surfaces and vulnerabilities. Generative AI tools and shadow AI implementations now pose significant data exposure risks that traditional security controls struggle to address. Employees increasingly use AI assistants to draft documents, analyze data, and automate tasks without IT oversight. These tools often upload sensitive business information to third-party servers, creating edge risks like Shadow AI/data require data-centric controls beyond conventional perimeter defenses. Organizations lose visibility into where their data travels and who can access it.
Traditional perimeter-based security architectures prove inadequate for modern distributed environments. Data loss prevention tools that monitor network boundaries miss threats originating from cloud services, mobile devices, and API integrations. Attackers exploit this gap by targeting data at rest in databases, in transit through APIs, and in use within applications. The shift to remote work, cloud infrastructure, and third-party integrations means that your data exists everywhere except behind your firewall, rendering perimeter controls largely ineffective.
Investing in security maturity and effective processes delivers better protection than simply increasing tool budgets. Research confirms that effective security depends on maturity and processes rather than just budget size or the number of security products deployed. Organizations that develop comprehensive policies, train employees thoroughly, and establish clear incident response procedures achieve superior outcomes compared to those that accumulate security tools without strategic implementation. Process maturity enables teams to use existing tools effectively rather than creating tool sprawl that nobody can manage properly.
| Security Approach | Coverage Scope | Effectiveness Against Modern Threats | Implementation Complexity |
|---|---|---|---|
| Perimeter DLP | Network boundaries only | Low for cloud and mobile data | Medium |
| Data-centric controls | Data wherever it resides | High across all environments | High |
| Process maturity focus | Organization-wide practices | Very high with proper execution | Medium to high |
| Tool accumulation | Fragmented point solutions | Low without integration | Very high |
Data-centric security strategies focus protection directly on information assets rather than network perimeters. This approach classifies data by sensitivity, applies appropriate controls based on classification, and monitors data access patterns regardless of location. Encryption protects data at rest and in transit. Access controls limit who can view or modify sensitive information. Data loss prevention monitors for unauthorized exfiltration attempts. Activity logging creates audit trails for compliance and investigation.
The complexity of modern threats requires organizations to adopt incremental improvement strategies rather than attempting wholesale security transformations. Building security maturity systematically through phased implementations allows teams to learn, adjust, and optimize each control before adding the next layer. This approach reduces implementation risks, spreads costs over time, and ensures that each security investment delivers measurable value before moving forward.
Pro Tip: Adopt incremental maturity models like the NIST Cybersecurity Framework to improve security systematically. Start by identifying your current maturity level, then focus on achieving the next level before pursuing advanced capabilities. This approach prevents overwhelming your team and ensures each security investment builds on solid foundations.
Organizations leveraging custom software development guide 2026 principles can build security directly into applications from the start. Security-by-design approaches cost less and work better than retrofitting protection into existing systems. Similarly, AI and machine learning services enable organizations to detect anomalous data access patterns and predict potential threats before they cause damage.
Implementing effective data security to protect digital assets
Business leaders face critical decisions about how much to invest in data security versus accepting certain risks. Not every threat warrants expensive countermeasures, and organizations must balance security spending against other business priorities. The key is making informed risk acceptance decisions based on threat likelihood, potential impact, and available mitigation options. Some risks merit acceptance when the cost of prevention exceeds the expected loss, while others demand immediate investment because the potential damage would be catastrophic.
Cybersecurity insurance has emerged as a valuable risk management tool that transfers some financial exposure to insurers. Policies typically cover breach response costs, legal fees, regulatory fines, and business interruption losses. However, insurers increasingly require organizations to demonstrate minimum security standards before issuing coverage. This trend pushes companies toward better security practices while providing financial protection against residual risks. The combination of strong security controls plus insurance coverage creates a more resilient risk management posture than either approach alone.
Many organizations struggle with diminishing returns on security investments after experiencing breaches. Studies show that many organizations face diminishing post-breach ROI, leading some to accept more risk or over-invest in redundant tools without improving actual security posture. The challenge lies in identifying which investments will genuinely reduce risk versus those that create security theater without substantive protection. Focusing on process maturity and policy effectiveness typically delivers better results than accumulating more security products.
Building mature security processes requires systematic attention to policies, procedures, training, and continuous improvement. Organizations should document clear security policies that define acceptable use, data handling requirements, and incident response procedures. Regular employee training ensures that everyone understands their security responsibilities. Tabletop exercises test incident response plans before real emergencies occur. Metrics and monitoring track security posture over time and identify areas needing improvement.
A practical implementation roadmap for strengthening data security includes:
- Conduct a comprehensive data inventory to identify what sensitive information you store and where it resides across your environment
- Classify data by sensitivity level and apply appropriate protection controls based on classification
- Implement strong access controls using the principle of least privilege to limit who can view or modify sensitive data
- Deploy encryption for data at rest in databases and data in transit across networks
- Establish monitoring and logging to detect unauthorized access attempts and suspicious activity patterns
- Develop and test incident response procedures so your team knows exactly what to do when security events occur
- Conduct regular security assessments and penetration testing to identify vulnerabilities before attackers exploit them
- Provide ongoing security awareness training to employees since human error causes the majority of breaches
Organizations pursuing custom software solutions UAE 2026 approaches gain opportunities to embed security controls directly into business applications. Custom development allows you to implement data protection measures that align precisely with your risk profile and compliance requirements. Off-the-shelf software often includes unnecessary features that expand your attack surface, while custom solutions include only what you need with security built in from the start.
Engaging IT consulting services provides access to specialized expertise that most organizations cannot afford to maintain in-house. Security consultants bring experience from working with hundreds of clients across various industries, allowing them to recommend proven approaches and help you avoid common implementation pitfalls. They can assess your current security posture objectively, identify gaps, and develop roadmaps for systematic improvement that align with your business objectives and budget constraints.
Protect your business with expert data security solutions
Securing your digital assets requires more than just installing security software. You need a strategic approach that aligns protection measures with business objectives while addressing your unique risk profile. YS Lootah Tech delivers comprehensive data security solutions tailored to your organization’s specific needs and industry requirements. Our team combines deep technical expertise with practical business understanding to design security programs that protect your assets without hindering productivity.
Our IT consulting services help you develop security strategies that make sense for your business. We assess your current posture, identify vulnerabilities, and create actionable roadmaps for improvement. Our data protection services implement robust controls that safeguard sensitive information across your entire environment. When you need custom solutions, our application development services build security directly into your software from the ground up. Contact us today to discuss how we can help protect your business assets.
Frequently asked questions
What makes data security essential for modern businesses?
Data security protects your most valuable assets from theft, corruption, and unauthorized access while enabling you to maintain customer trust and meet regulatory requirements. Without adequate security, you risk massive financial losses, operational disruption, and permanent damage to your reputation that can destroy your competitive position.
How do data breaches impact businesses beyond immediate financial costs?
Breaches destroy customer trust, causing up to 80% of affected customers to switch to competitors. They damage your brand reputation for years, increase customer acquisition costs, create competitive disadvantages, and force you to invest heavily in remediation and brand rehabilitation while dealing with extended operational disruptions.
What security approach works best for protecting data in cloud environments?
Data-centric security strategies that protect information wherever it resides work best for cloud environments. Focus on data classification, encryption, access controls, and activity monitoring rather than perimeter defenses. Implement data protection services that follow your data across all locations and platforms.
Should organizations invest more in security tools or security processes?
Security processes and maturity deliver better protection than simply accumulating more tools. Effective policies, employee training, incident response procedures, and systematic improvement programs outperform tool sprawl. Invest in processes first, then add tools strategically to support those processes rather than the reverse.
How can small businesses afford adequate data security protection?
Small businesses should focus on high-impact, low-cost security fundamentals like strong passwords, multi-factor authentication, regular backups, employee training, and basic access controls. Leverage managed security services and cloud providers that include security features. Prioritize protecting your most sensitive data rather than attempting to secure everything equally.