What is IT security? Protecting business data explained

TL;DR:
- IT security is a comprehensive approach that includes physical, administrative, and technical controls beyond just cybersecurity. Implementing proven frameworks like NIST CSF and CIS Controls, along with fundamental principles like defense in depth and least privilege, significantly reduces organizational risk. Building a security-aware culture and continuous management are essential for effective protection against modern, evolving threats.
Most business owners think IT security means strong passwords and a firewall. That view leaves enormous gaps. IT security protects information systems, networks, and data from unauthorized access, disruption, and destruction, covering far more ground than most realize. It spans physical controls, administrative policies, and technical safeguards working together. This guide breaks down what IT security actually covers, which frameworks give you the strongest foundation, how modern threats bypass even solid defenses, and what steps turn security knowledge into measurable protection for your business.
Table of Contents
- Defining IT security: More than just cybersecurity
- Core frameworks and principles: Building secure foundations
- Modern threats, edge cases, and why tools can fail
- Business impact and applying IT security for results
- Why most IT security advice falls short—and what actually works
- How YS Lootah Tech helps secure your business
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Broader than cybersecurity | IT security includes physical, administrative, and technical controls beyond the digital realm. |
| Frameworks guide action | Using NIST CSF or CIS Controls provides a solid, proven foundation for protecting business assets. |
| Modern threats evolve fast | New attack methods and bypasses mean organizations must regularly update and review their defenses. |
| Quick wins are possible | Implementing basic steps like asset inventory and MFA dramatically reduces risk for most businesses. |
| Culture beats complexity | Results depend on engaged leadership and staff, not just technical solutions or checklists. |
Defining IT security: More than just cybersecurity
There is a common assumption that IT security and cybersecurity are the same thing. They are not. IT security is broader than cybersecurity and includes physical, administrative, and technical controls. Cybersecurity is a subset that focuses specifically on defending digital systems and online assets from attacks. IT security, by contrast, also covers who can walk into your server room, how paper documents are stored and destroyed, and which employees have access to sensitive systems.
Understanding cybersecurity vs IT security helps clarify where your organization may have blind spots. A business can have excellent antivirus software and still suffer a breach because a contractor left a server cabinet unlocked or a printed client list was left on a desk.
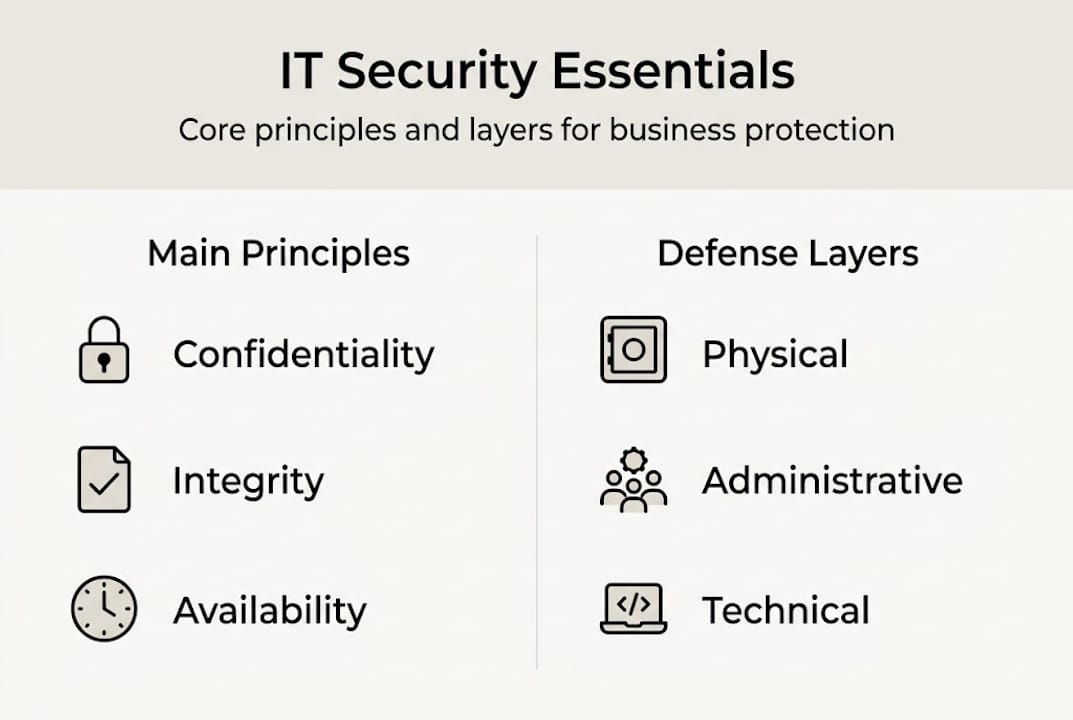
At the core of IT security sit three principles known as the CIA triad:
- Confidentiality: Only authorized people can access sensitive information.
- Integrity: Data is accurate and has not been tampered with.
- Availability: Systems and data are accessible when needed by the right people.
These three principles apply equally to digital files, physical records, and the systems that process them.
| Dimension | IT security | Cybersecurity |
|---|---|---|
| Scope | Physical, administrative, technical | Digital and online systems |
| Examples | Server room locks, access policies, encryption | Firewalls, antivirus, intrusion detection |
| Business impact | Holistic risk reduction across all assets | Focused protection of digital infrastructure |
Common misconceptions about IT security:
- It is only an IT department problem.
- Antivirus software is sufficient protection.
- Small businesses are not targets.
- Security is a one-time project, not an ongoing process.
- Compliance equals security.
"IT security is not just digital firewalls. It is business resilience, covering every layer of how your organization stores, moves, and protects its most valuable information."
For practical data security steps that go beyond software tools, the physical and administrative layers deserve equal attention from leadership.
Core frameworks and principles: Building secure foundations
With a clearer understanding of what IT security covers, practical frameworks make building strong defenses possible. Two frameworks stand out for business use: the NIST Cybersecurity Framework (CSF 2.0) and the CIS Controls v8.1. Both are widely adopted and designed to be practical regardless of company size.
The NIST CSF and CIS Controls give organizations structured ways to identify risks, protect assets, detect threats, respond to incidents, and recover from disruptions. They are not competing approaches. Many businesses use both together.

| Framework | Core purpose | Key highlights |
|---|---|---|
| NIST CSF 2.0 | Risk-based security governance | Six functions: Govern, Identify, Protect, Detect, Respond, Recover |
| CIS Controls v8.1 | Prioritized, actionable controls | 18 controls organized by implementation group |
Three secure design principles underpin both frameworks:
- Defense in depth: Layer multiple controls so that if one fails, others remain.
- Least privilege: Users and systems get only the access they need to do their jobs, nothing more.
- Separation of duties: No single person controls an entire critical process, reducing fraud and error risk.
Steps to start with basic (IG1) security controls:
- Build an inventory of all hardware and software assets.
- Configure devices securely using established benchmarks.
- Manage user accounts and remove inactive ones regularly.
- Enable audit logging on critical systems.
- Implement automated patch management.
- Restrict administrative privileges to essential personnel only.
Implementing the first 6 to 8 CIS Controls reduces organizational risk by approximately 80%. That is a significant return for steps that do not require large budgets.
Pro Tip: Before buying any new security tool, complete your asset inventory first. You cannot protect what you do not know exists. Many businesses discover forgotten servers, old employee accounts, and unmanaged devices during this process, each one a potential entry point.
For a deeper look at how security frameworks in business translate into daily operations, the connection between governance and technical controls becomes clear. An executive cybersecurity workflow can help leadership take ownership of these priorities without getting lost in technical detail.
Modern threats, edge cases, and why tools can fail
Frameworks are only effective if they address how today's threats actually operate. The threat landscape has shifted significantly, and traditional perimeter defenses are no longer enough.
Zero Trust is a security model that assumes no user, device, or network segment is automatically trusted, even inside your own organization. Zero Trust goes beyond traditional perimeter security by requiring continuous verification at every access point. This matters because attackers increasingly operate from inside networks, using stolen credentials or compromised devices.
Supply chain attacks add another layer of complexity. Instead of attacking your business directly, adversaries compromise a vendor or software provider you trust. The result is that your defenses never see the threat coming because it arrives through a legitimate channel. AI-driven threats and supply chain attacks are outpacing traditional defenses, and 90% of organizations lack true security maturity to counter them.
For a full picture of what is changing, the top cybersecurity trends shaping 2026 show just how quickly the attack surface is expanding.
Common bypass methods attackers use:
- Weak or reused passwords with no multi-factor authentication.
- Social engineering and phishing targeting employees directly.
- Unpatched software with known vulnerabilities.
- Misconfigured cloud storage exposing sensitive data publicly.
- Third-party vendor access with excessive permissions.
Understanding cybersecurity in 2026 means accepting that technology alone will not close these gaps. Tools fail when people are not trained, when processes are not followed, and when leadership treats security as a checkbox rather than a continuous practice.
Pro Tip: Employee awareness training is not optional. The majority of successful attacks begin with a human action, whether clicking a phishing link or sharing credentials. A well-trained team is one of the most cost-effective defenses available. Pairing training with technical controls like IT support services creates a much stronger combined defense.
Business impact and applying IT security for results
Understanding threats is crucial. Knowing how to turn security practices into real-world protection is where results happen.
Breaches are expensive. Direct costs include forensic investigation, legal fees, regulatory fines, and customer notification. Indirect costs include lost business, reputational damage, and operational downtime. Mature security programs can reduce the likelihood of a significant breach by up to 69%, making investment in security far cheaper than recovering from an incident.
Practical steps for business owners and IT managers:
- Enable multi-factor authentication on all critical accounts and systems.
- Patch operating systems and applications on a regular, documented schedule.
- Complete and maintain a full asset inventory updated at least quarterly.
- Segment your network so that a breach in one area does not spread freely.
- Test your incident response plan before you need it.
Key business benefits of strong IT security:
- Reduced financial exposure from breaches and regulatory fines.
- Stronger customer trust and competitive differentiation.
- Smoother compliance with industry regulations and standards.
- Faster recovery from incidents due to tested response plans.
- Greater operational continuity and reduced downtime risk.
For a practical breakdown of cybersecurity best practices that translate directly to business outcomes, the focus should always be on reducing real risk, not just passing audits.
"The top 4% of mature security programs reduce breach likelihood by nearly 70%, proving that consistent, disciplined execution of fundamentals outperforms expensive tools used inconsistently."
Understanding why protecting business assets requires a layered approach helps leadership make smarter budget decisions and avoid the false comfort of single-point solutions.
Why most IT security advice falls short—and what actually works
Here is an uncomfortable truth: most organizations that experience serious breaches had a security policy in place. They had tools. They had frameworks. What they lacked was a culture where security was practiced, not just documented.
Checklists and frameworks are starting points, not destinations. When security becomes a compliance exercise, teams check boxes without understanding why. Controls get implemented poorly. Exceptions pile up. Gaps form in places no audit catches.
Executive buy-in is not just about budget approval. It means leadership visibly participates in security practices, asks hard questions in reviews, and treats a near-miss as seriously as an actual incident. When leadership disengages, the rest of the organization follows.
The most effective programs we have seen share one trait: they start simple and stay consistent. A complete asset inventory combined with regular employee training outperforms a complex, expensive security stack that nobody fully understands or follows.
Looking at security frameworks in action confirms that execution quality matters more than framework sophistication.
Pro Tip: The best security program is the one your entire team actually follows, not the most technically complex one on paper.
How YS Lootah Tech helps secure your business
Putting these principles into practice requires more than good intentions. It requires the right partner.
At YS Lootah Tech, we build security into every layer of what we deliver. From secure application development that follows least-privilege and defense-in-depth principles to AI and machine learning solutions that help detect threats before they escalate, our team brings both technical depth and strategic clarity to your security challenges. Whether you need a full security assessment, a custom application built with modern safeguards, or ongoing consultation to strengthen your IT posture, we are ready to help. Reach out today to start the conversation.
Frequently asked questions
What is the difference between IT security and cybersecurity?
IT security includes physical and administrative safeguards alongside technical ones, while cybersecurity focuses specifically on protecting digital and online assets. Think of cybersecurity as one important layer within the broader IT security picture.
What are the key components of IT security?
The core components are confidentiality, integrity, and availability, known as the CIA triad. These three principles apply to every type of information your business handles, whether digital or physical.
Why is asset inventory important in IT security?
Asset inventory is foundational because you cannot protect what you do not know exists. It gives your team a complete picture of what needs to be secured and where the highest risks sit.
How can basic security controls reduce risk for businesses?
Applying the first 6 to 8 CIS Controls reduces risk by approximately 80%, making them the highest-return starting point for any organization building or improving its security posture.
What is Zero Trust security?
Zero Trust requires continuous verification of every user and device rather than assuming anything inside the network is safe. It significantly reduces risk from both external attackers and compromised internal accounts.