Executive cybersecurity workflow: reduce risk in 5 steps

TL;DR:
- An executive-driven cybersecurity workflow aligns risk management with business priorities, enhancing resilience.
- Frameworks like NIST CSF, CIS Controls, and MITRE ATT&CK guide structured governance and threat defense.
- Measuring and storytelling about risk, using KPIs and financial impact, strengthens board support and program effectiveness.
A single unpatched server. One misconfigured access policy. These are the entry points that cost enterprises millions and land executives on the front page for the wrong reasons. Cybersecurity failures are no longer purely technical events; they are governance failures that regulators, boards, and shareholders trace directly to leadership. The average cost of a data breach now exceeds $4.8 million, and recovery timelines stretch well beyond the incident itself. This guide walks you through a structured, executive-driven cybersecurity workflow covering governance, risk prioritization, control execution, and ongoing verification so your organization builds measurable resilience instead of reactive chaos.
Table of Contents
- Understand the cybersecurity workflow landscape
- Prepare: Governance, risk assessment, and asset inventory
- Execute: Prioritize and implement controls for measurable impact
- Verify: Measure effectiveness, report, and adapt
- Why a strategic and storytelling approach unlocks real executive impact
- How YS Lootah Tech can accelerate your cybersecurity workflow
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Use structured frameworks | Frameworks like NIST CSF, CIS Controls, and MITRE ATT&CK provide executives with proven workflows and clear steps to reduce risk. |
| Prioritize governance and asset inventory | A strong governance model and full asset inventory are essential for effective risk management and control selection. |
| Implement high-impact controls first | Focusing on foundational controls such as IG1 rapidly increases maturity and lowers top risks. |
| Monitor with business-aligned KPIs | Tracking metrics like MFA coverage, MTTR, and cost avoidance demonstrates value and drives ongoing improvement. |
| Tell the risk story | Executive success depends on translating security efforts into financial impact, resilience, and board-ready narratives. |
Understand the cybersecurity workflow landscape
Most organizations treat cybersecurity as an IT department problem. That assumption is exactly what attackers count on. When executives own the workflow, security decisions align with business priorities, budgets move faster, and accountability is clear. An executive-driven cybersecurity workflow is a repeatable, structured process that connects risk identification to control deployment to board-level reporting.
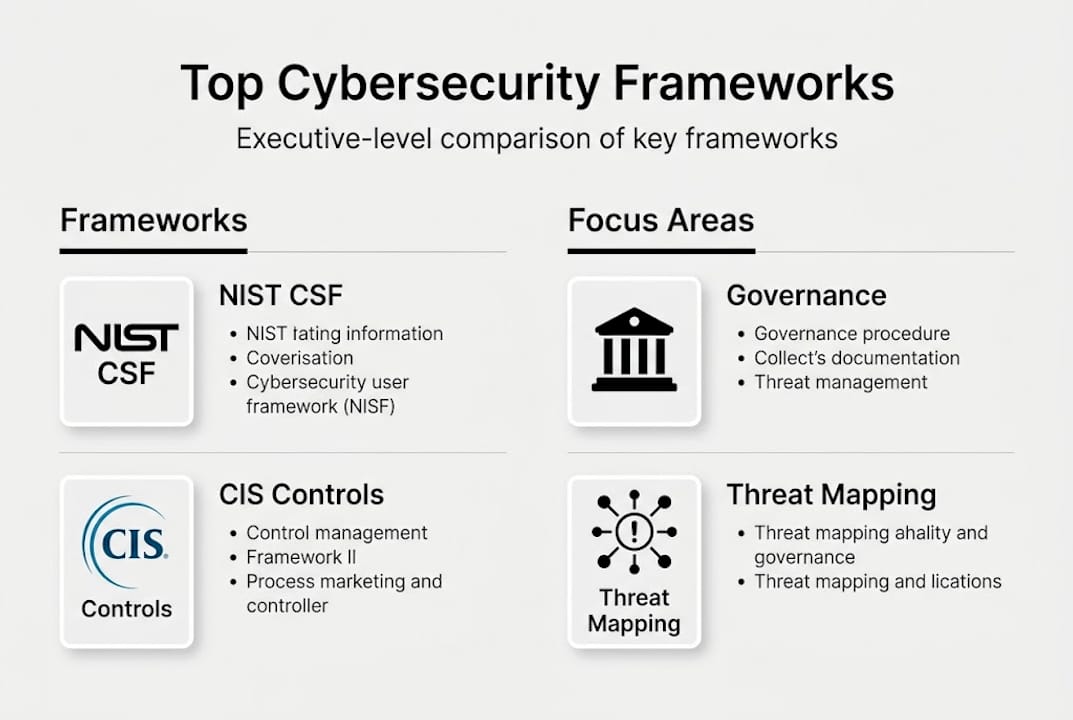
Three frameworks dominate the enterprise space, and each serves a distinct purpose. NIST CSF 2.0, CIS Controls v8, and MITRE ATT&CK are the recommended starting points for structuring workflows at the executive level. Understanding what each one does prevents the common mistake of adopting all three without a clear integration strategy.
| Framework | Primary use | Executive value |
|---|---|---|
| NIST CSF 2.0 | Govern, Identify, Protect, Detect, Respond, Recover | Risk-aligned governance language |
| CIS Controls v8 | Prioritized technical controls (IG1 to IG3) | Measurable maturity progression |
| MITRE ATT&CK | Adversary tactics and techniques mapping | Threat-informed defense decisions |
CIS Controls v8 organizes controls into three Implementation Groups. IG1 covers basic cyber hygiene for all organizations. IG2 adds controls for organizations handling sensitive data. IG3 addresses the most sophisticated threat environments. Enterprises that benchmark against these groups report an average NIST CSF coverage rate of 70.7%, meaning most organizations have meaningful gaps even when they believe their programs are mature.
The contrast between ad hoc and structured approaches is stark. Ad hoc security generates inconsistent controls, unclear ownership, and no baseline for measuring improvement. Structured workflows, by contrast, produce repeatable processes, auditable evidence, and a shared language between IT teams and the board. Reviewing enterprise cybersecurity best practices gives you a practical starting point for translating framework theory into operational steps.
Key workflow stages every executive should recognize:
- Govern: Define risk appetite, assign accountability, establish policy
- Identify: Map assets, assess risks, understand the threat landscape
- Protect: Deploy prioritized controls based on maturity level
- Detect: Monitor for anomalies and threat indicators continuously
- Respond and Recover: Execute tested plans and measure recovery speed
For a deeper look at how strategic protection approaches connect to business outcomes, the distinction between reactive and proactive postures becomes clear quickly. Executives who invest in security frameworks explained for their leadership teams consistently report faster board alignment and stronger budget cases.
Prepare: Governance, risk assessment, and asset inventory
Governance is not a policy document sitting in a shared drive. It is the active, executive-led process of defining who owns risk decisions, what the organization's risk appetite actually is, and how accountability flows from the board to operational teams. NIST Govern and CIS RAM form the core of this preparation phase, giving executives a structured method to assess risk in business terms rather than technical jargon.
Follow these steps to build a solid preparation foundation:
- Establish governance structure. Assign a named executive owner for cybersecurity risk. Define escalation paths, board reporting cadence, and policy approval authority.
- Conduct a formal risk assessment. Use CIS RAM to score risks by likelihood and business impact. Involve finance and operations, not just IT.
- Build a comprehensive asset inventory. Catalog every digital asset including cloud workloads, third-party integrations, and operational technology. Assign a business owner to each asset category.
- Define risk appetite thresholds. Translate technical risk scores into financial exposure ranges the board can act on.
- Establish accountability checkpoints. Set quarterly reviews where asset owners report status to executive leadership.
Here is a simplified asset and risk mapping snapshot to illustrate how this looks in practice:
| Asset category | Business owner | Risk score (CIS RAM) | Financial exposure |
|---|---|---|---|
| Customer data platform | Chief Revenue Officer | High | $2.1M potential breach cost |
| ERP system | Chief Financial Officer | Critical | $4.5M operational disruption |
| OT/SCADA network | VP Operations | High | $6.8M production downtime |
| Cloud infrastructure | Chief Technology Officer | Medium | $1.2M recovery cost |
Three questions every executive must be able to answer before moving forward: What is our defined risk appetite? Who is accountable to the board for each major asset? What triggers an escalation to leadership?

Pro Tip: Align your asset listings with financial and operational impact, not just IT classification. An asset that IT rates as "medium" may be mission-critical from a revenue or regulatory perspective. Cross-referencing with finance closes that gap fast.
For actionable governance steps that connect policy to practice, the key is making governance visible and measurable. A solid data security inventory process also ensures you are not protecting assets you have forgotten you own, which is a more common problem than most executives realize.
Execute: Prioritize and implement controls for measurable impact
Preparation without execution is just planning. This phase is where executive leadership translates risk assessments into deployed controls with clear owners, timelines, and success metrics. The CIS Controls framework makes prioritization straightforward because the maturity levels tell you exactly where to start.
Follow this execution sequence:
- Identify your IG1 priority controls. These cover inventory management, access control, data protection, and vulnerability management. They address the highest-frequency attack vectors.
- Assign implementation teams with executive sponsors. Each control group needs a named owner and a budget line. Ambiguity here is where programs stall.
- Set a 90-day sprint for IG1 completion. Short cycles create accountability and visible progress for board reporting.
- Scale to IG2 controls once IG1 is verified. Add endpoint detection, audit log management, and email/web gateway protections.
- Monitor progress weekly using a shared dashboard visible to executive leadership and IT leads.
Prioritized controls like IG1 for basic hygiene, measured through KPIs including MFA coverage, patch latency, and mean time to respond (MTTR), are what separate organizations that improve from those that stagnate. An energy sector organization following this approach reached CIS maturity in eight months and reduced incidents by 40% while improving its SecurityScorecard rating by 18 points and saving $7,000 annually on cyber insurance premiums.
Executive KPI dashboard targets: MFA coverage at or above 98% across all privileged accounts. Patch latency reduced to under 15 days for critical vulnerabilities. MTTR below 4 hours for high-severity incidents. SecurityScorecard improvement of 15 or more points within 12 months. Cyber insurance premium reduction as a financial proof point.
Pro Tip: Start with IG1 controls and resist the temptation to jump to advanced tooling. Organizations that skip foundational hygiene and invest in sophisticated detection tools often find that basic gaps undermine expensive capabilities. Fix the fundamentals first.
For teams looking to deepen their approach, implementing best practices and understanding how CIS Controls for resilience map to business outcomes gives executive sponsors the language they need to maintain board confidence throughout the program.
Verify: Measure effectiveness, report, and adapt
Controls that are deployed but never measured create a false sense of security. Verification is the phase most organizations underinvest in, and it is exactly where mature programs separate themselves. Executive oversight at this stage means owning the metrics, not just receiving a report.
Key KPIs for executive dashboards:
- MTTR (mean time to respond): Measures how fast your team contains threats
- Vulnerability aging: Tracks how long known weaknesses remain unpatched
- MFA coverage rate: Confirms identity protection across all critical systems
- Cost avoidance: Quantifies incidents prevented relative to potential breach costs
- Cyber insurance savings: Demonstrates financial ROI of the security program
- Third-party risk scores: Monitors supplier security posture continuously
Boards want business-aligned risk stories rather than technical metrics, and automating data collection enables continuous monitoring without burdening security teams with manual reporting cycles. The shift from spreadsheet-based reporting to automated dashboards is one of the highest-leverage moves an executive can make.
Here is how to structure board-ready reporting:
| Report element | What to include | Why it matters |
|---|---|---|
| Risk narrative | Top 3 risks and mitigation status | Connects security to business strategy |
| Financial impact | Cost avoidance, insurance savings | Justifies budget and program investment |
| Control coverage | IG1/IG2 completion percentage | Shows measurable program maturity |
| Incident summary | Count, MTTR, root cause themes | Demonstrates operational effectiveness |
Adaptation is not optional. OT/IT convergence, AI-powered attacks, and supply chain vulnerabilities are reshaping the threat landscape faster than annual reviews can track. Reviewing cybersecurity trends quarterly and incorporating automation in measurement ensures your workflow evolves with the threat environment rather than lagging behind it. For AI-specific threats, MITRE ATLAS for AI threats provides a structured modeling approach that is increasingly relevant for enterprises using AI-driven operations.
Pro Tip: Use quarterly board reports as a budget alignment tool, not just a compliance exercise. Executives who frame security metrics in terms of risk appetite and financial exposure consistently secure more program autonomy and faster approval for critical investments.
Why a strategic and storytelling approach unlocks real executive impact
Here is what most cybersecurity guides will not tell you: technical controls are necessary but not sufficient. The executives who build the most resilient programs are not the ones with the most sophisticated tools. They are the ones who can tell a compelling story about risk.
The world's most effective CISOs use heat maps, ROI calculations, and financial translation to shift security from a cost center narrative to a value creation story. When a board member sees that a $400,000 security investment prevented a projected $4.2 million breach, the conversation changes. Budget requests stop being defended and start being anticipated.
Risk monetization is the skill that separates good security leaders from great ones. Quantifying risk in dollar terms, using models like FAIR (Factor Analysis of Information Risk), gives executives a shared language with finance and the board. It also forces precision. You cannot monetize a vague threat. You have to understand your assets, your exposures, and your controls well enough to put a number on them.
Regular board engagement, not just quarterly reporting, builds the trust that earns program autonomy. Executives who brief their boards informally between formal cycles report fewer budget surprises and stronger cross-functional support. Reviewing executive storytelling examples shows how leading organizations frame security as a strategic asset rather than an operational burden. Own the narrative and you own the program.
How YS Lootah Tech can accelerate your cybersecurity workflow
Building an executive-driven cybersecurity workflow requires more than frameworks and good intentions. It requires the right technical partner who understands both the strategic and operational dimensions of enterprise security.
YS Lootah Tech works with medium to large enterprises across the Middle East to design and implement structured cybersecurity programs aligned with NIST CSF 2.0, CIS Controls, and board-level governance requirements. From enterprise website development built with security by design to application development solutions that integrate compliance controls from the ground up, our team brings end-to-end expertise. Whether you need a full workflow implementation or executive advisory support, contact YS Lootah Tech to schedule a strategy session tailored to your organization's risk profile and growth objectives.
Frequently asked questions
What are the top frameworks for executive-led cybersecurity workflows?
NIST CSF 2.0, CIS Controls v8, and MITRE ATT&CK are the recommended frameworks for structuring executive-level cybersecurity workflows, each addressing governance, control prioritization, and threat modeling respectively.
Which KPIs should executives track to measure cybersecurity program success?
Critical KPIs include MFA coverage, patch latency, and MTTR, along with cost avoidance and incident reduction rate, which together give executives a complete picture of program health.
How often should cybersecurity performance be reported to the board?
Quarterly reporting is the recommended cadence, using business-oriented language that connects security metrics to risk appetite alignment and financial exposure rather than technical detail.
What is the benefit of starting with basic controls (IG1)?
IG1 controls address the most common attack vectors and deliver the fastest risk reduction, creating a verified foundation before organizations invest in more advanced capabilities.
How can automation support executive oversight of cybersecurity workflows?
Automation streamlines KPI collection and enables continuous monitoring, removing manual reporting bottlenecks and ensuring executives receive timely, accurate data for decision-making.