Cybersecurity Fundamentals Explained: Guide for Dubai Leaders

TL;DR:
- Most Dubai breaches result from missed basics like unpatched systems and human error.
- Implementing foundational controls such as asset inventory and MFA provides high security returns.
- Emphasizing leadership oversight and continuous improvement is key to cybersecurity resilience.
Most major breaches hitting Dubai organizations right now trace back not to nation-state hackers or zero-day exploits, but to missed basics. An untracked device here, an unpatched server there, and suddenly sensitive data is gone. Human error remains the leading cause of breaches, not sophisticated attacks. This guide breaks down cybersecurity fundamentals in plain language, walking you through the frameworks, controls, and leadership actions that matter most. Whether you are a CISO in a Dubai bank or a business leader overseeing IT for a regional enterprise, these essentials give you the clarity to act confidently.
Table of Contents
- Understanding cybersecurity frameworks: The backbone of resilience
- Core controls every Dubai business must master
- Emerging risks and overlooked gaps in 2026
- Making cybersecurity fundamentals actionable in Dubai
- The uncomfortable truth about cybersecurity maturity
- How YS Lootah Tech helps secure your digital future
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
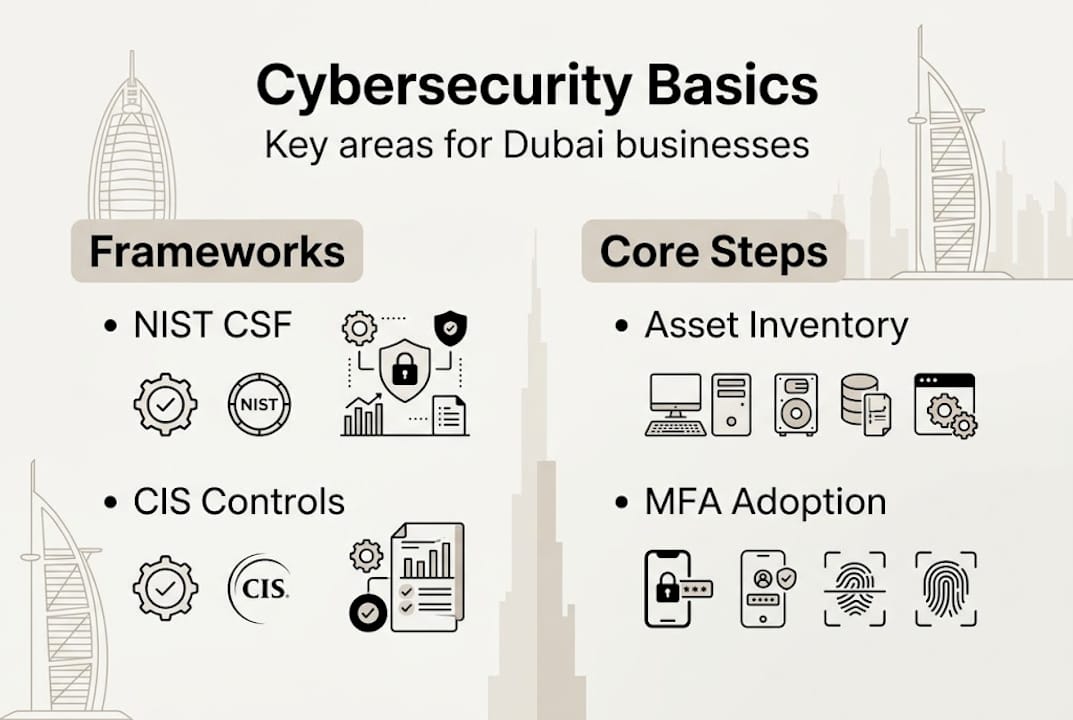
| Start with frameworks | NIST CSF 2.0 and CIS Controls provide a solid, scalable base for all Dubai businesses. |
| Prioritize basic controls | Focusing on asset inventory, MFA, and patching blocks most cyber attacks. |
| Watch for emerging risks | Human error and supply chain gaps cause more breaches than advanced threats. |
| Make it actionable | Link board oversight to security priorities for effective, measurable improvement. |
Understanding cybersecurity frameworks: The backbone of resilience
Think of a cybersecurity framework as a shared language between your IT team and your boardroom. It gives everyone a structured way to identify risks, apply controls, and measure progress. Without one, security efforts become reactive and fragmented. With the need for clarity on fundamentals established, let's demystify the frameworks that underpin today's strongest security strategies.
Three frameworks lead the conversation in 2026:
- NIST CSF 2.0: The National Institute of Standards and Technology updated its Cybersecurity Framework with a new sixth function. The NIST CSF 2.0 revision adds the Govern function alongside Identify, Protect, Detect, Respond, and Recover, placing policy and executive oversight at the center of security strategy.
- CIS Controls v8.1: The CIS Controls organize 18 controls into three implementation groups (IG1, IG2, IG3), so organizations can scale their security posture from essential basics to advanced maturity.
- CISA CPGs v2.0: The Cybersecurity and Infrastructure Security Agency's Cross-Sector Performance Goals offer a quick-start set of controls aligned to NIST, designed specifically for critical sectors like finance, energy, and healthcare.
For Dubai organizations, the choice depends on your sector and starting point. A financial institution may prioritize NIST CSF 2.0 for its governance focus. A smaller enterprise getting started benefits more from security frameworks explained through the lens of CIS IG1. CISA CPGs work well for quick benchmarking across any industry.
| Framework | Best for | Key feature |
|---|---|---|
| NIST CSF 2.0 | Mid to large enterprises | Six functions including Govern |
| CIS Controls v8.1 | All sizes | 18 controls, three IG tiers |
| CISA CPGs v2.0 | Critical sectors | Quick-start, NIST-aligned |
Pro Tip: Before selecting a framework, map your current security activities to NIST CSF 2.0's six functions. Gaps will become visible almost immediately, giving you a practical starting point rather than a theoretical one.
The Govern function in NIST CSF 2.0 is arguably the most important addition for executive teams. It formalizes the role of leadership in setting cybersecurity policy, managing risk tolerance, and maintaining accountability. For Dubai leaders who want to read more, the cybersecurity strategy for 2026 provides a sharper view of where this is all heading.
Core controls every Dubai business must master
Knowing the frameworks is step one. Now, let's uncover the controls that provide the greatest security return on investment.
The 18 CIS Controls cover everything from asset inventory to penetration testing. But not all controls are equal in impact. For most Dubai organizations, the following six deliver the strongest immediate protection:
- Asset inventory: You cannot protect what you cannot see. Every device, application, and data store must be cataloged.
- Multi-factor authentication (MFA): A single extra verification step blocks a significant portion of credential-based attacks.
- Secure configuration: Default settings on devices and software are rarely secure. Lock them down before deployment.
- Patch management: Unpatched systems are open doors. Establish a regular patching cadence, weekly for critical systems.
- Access control: Limit permissions to what each role actually needs. Excessive access is a liability.
- Incident response (IR): A documented, tested IR plan turns a crisis into a manageable event.
The CIS Controls mitigate the majority of attacks when basic and foundational controls are implemented consistently. IG1, the essential tier, covers 56 safeguards across the first six controls and is specifically designed to protect organizations against the most common attacks.

Here's a sobering benchmark: only 4% of organizations are classified as mature in cyber readiness according to the 2025 Cisco Cybersecurity Readiness Index. That means 96% of businesses, including many in Dubai, are still building the basics.
| Control group | CIS tier | Key safeguards |
|---|---|---|
| Asset inventory | IG1 | Hardware and software tracking |
| MFA | IG1 | All user accounts, especially admin |
| Patch management | IG1 | Monthly cadence minimum |
| Access control | IG2 | Least privilege, role-based access |
| Incident response | IG2 | Documented, tested annually |
A quick-start sequence for your team:
- Audit all devices and software in your environment this week.
- Enable MFA on every admin and privileged account immediately.
- Run a patch audit and remediate critical vulnerabilities within 30 days.
- Review user permissions and remove unnecessary access.
- Schedule a tabletop incident response exercise this quarter.
For deeper guidance, the cybersecurity best practices resource and data protection for Dubai businesses cover these controls in detail. If your organization uses cloud infrastructure, understanding cloud security benefit is equally essential.
Pro Tip: MFA and asset visibility together resolve more than half of the common attack vectors facing Dubai businesses today. Start there before anything else.
Emerging risks and overlooked gaps in 2026
With the essentials covered, it's critical to address why breaches still happen and what new risks are emerging in 2026.
The assumption that advanced firewalls and perimeter security are enough is outdated and dangerous. The 2025 threat landscape exposed something uncomfortable: the very tools organizations trusted most became the weakest links.
"2025 was the year the edge collapsed. VPNs and firewalls, long considered the first line of defense, became primary breach entry points. Supply chain attacks multiplied and human error topped breach causes, often outpacing technically sophisticated exploits."
This matters for Dubai organizations because many still rely heavily on perimeter security models. When an attacker compromises a VPN appliance or exploits a misconfigured firewall, they bypass all the internal controls behind it.
Emerging risks your organization must monitor in 2026:
- Supply chain compromise: A vendor with weak security becomes your problem. Require security assessments from all third-party software and service providers.
- AI-assisted phishing: Generative AI now produces near-perfect phishing emails in Arabic and English, making user awareness training more critical than ever.
- Unmanaged edge devices: IoT sensors, remote access tools, and cloud gateways are expanding attack surfaces beyond traditional IT boundaries.
- Credential stuffing: Stolen credentials from previous breaches are reused constantly. Password hygiene and MFA are your direct counter.
- Insider threats: Deliberate or accidental, employees with excessive access remain a persistent risk.
The good news is that strong fundamentals counter most of these threats. An accurate asset inventory catches unmanaged edge devices. MFA stops credential stuffing. Patch management closes the vulnerabilities that supply chain attackers exploit. For leaders who want a structured approach to managing these risks, the executive risk reduction workflow and cybersecurity trends for 2026 both offer practical perspectives tailored to the regional context.
Making cybersecurity fundamentals actionable in Dubai
Understanding gaps and risks equips you, but how do you put these fundamentals into practice? Here's how Dubai leaders can take action today.
The most common failure mode is analysis paralysis. Organizations spend months selecting frameworks and designing policies while real vulnerabilities remain open. The antidote is a structured, sequenced approach that starts with governance and moves quickly to technical action.
A practical sequence for Dubai business leaders:
- Activate Govern first: Assign a named executive owner for cybersecurity. Define your risk appetite in writing. Make it a boardroom conversation, not just an IT concern.
- Complete asset inventory: Within the first 30 days, catalog every device, cloud service, and application your organization uses.
- Deploy MFA: Roll it out to all privileged accounts in week one, then extend to all staff within 60 days.
- Establish patch cycles: Define cadences based on criticality. Critical patches within 72 hours, routine patches monthly.
- Benchmark with CISA CPGs: Use the CPG checklist to identify gaps quickly without needing a full framework implementation.
- Build a security culture: Monthly awareness sessions, simulated phishing tests, and clear reporting channels turn staff from a liability into a defense layer.
Leadership engagement is not optional. The NIST CSF 2.0 Govern function exists precisely because technical controls fail without executive alignment. When the board tracks cybersecurity as a key performance indicator, investment follows and teams are accountable.
For Dubai organizations navigating this alongside broader operational shifts, the digital strategy tips and digital transformation guidance offer relevant context on integrating security into growth strategies.
Pro Tip: Add a cybersecurity KPI to your quarterly board pack. Track patch coverage, MFA adoption rate, and open critical vulnerabilities. What gets measured gets improved.
The uncomfortable truth about cybersecurity maturity
Here is something most vendors will not tell you: cybersecurity perfection does not exist, and chasing it wastes resources that could fix real problems. The organizations we see struggling most are often those that invest heavily in advanced solutions before sorting out asset inventory or enforcing MFA.
Only 4% of organizations are considered mature in cyber readiness. That statistic is not an indictment of effort. It reflects a common mistake: prioritizing complexity over coverage. One overlooked server without patches can negate a six-figure investment in threat intelligence tooling.
Progress beats perfection every time. Start with the essential cybersecurity perspective that resilience is built incrementally, not purchased as a product. Dubai leaders who commit to continuous improvement across the basics will outperform those waiting for a perfect security program that never arrives. Cover the essentials well, review them regularly, and build from there.
How YS Lootah Tech helps secure your digital future
Ready to turn security fundamentals into a genuine competitive advantage? YS Lootah Tech works with organizations across Dubai and the wider region to move from security awareness to security action.
Our team brings practical expertise in secure application development and secure website development, ensuring that every digital product your organization builds starts with security by design. We also deploy AI-powered security solutions that help teams detect and respond to threats faster than traditional methods allow. From strategy workshops to hands-on implementation, we tailor every engagement to the size, sector, and risk profile of your organization. Contact us to turn the fundamentals covered in this guide into measurable, lasting protection for your business.
Frequently asked questions
Which cybersecurity framework is best for Dubai businesses to start with?
Most Dubai firms benefit from starting with NIST CSF 2.0 or CIS IG1, both of which offer risk-based, scalable guidance suited to any industry size or sector.
What first steps should leadership teams take to improve cybersecurity?
Prioritize asset inventory, multi-factor authentication, and board-level oversight as your first actions. Quick wins include Govern setup, asset inventory, MFA rollout, and regular patching benchmarked against CISA CPGs.
How do human errors impact cybersecurity threats today?
Human error tops breach causes, often bypassing even advanced technical defenses, making staff awareness and controlled access more important than any single technology.
Why are edge systems like firewalls and VPNs especially vulnerable?
Edge systems are the first point of contact in most attacks, and edge collapse in 2025 showed firewalls and VPNs failing early, before internal network controls could respond.
What's the best way to benchmark security progress for a Dubai organization?
Benchmark against CISA CPGs or CIS Control Implementation Groups for sector-relevant priorities. Both tools are designed to measure and guide progress in practical, actionable terms.