Cybersecurity in 2026: Protecting organizations strategically

Cybercrime is no longer a background IT concern. It is a board-level business risk that reshapes competitive landscapes, destroys customer trust, and triggers regulatory consequences that can take years to recover from. Cybercrime costs equal 3% of GDP in advanced economies, and optimal investments can avert $3.3 trillion in damages. For business leaders and IT professionals, the question is no longer whether to prioritize cybersecurity, but how to make it work as a strategic asset rather than a reactive expense. This article breaks down the real threats, the leading frameworks, and the practical steps that move organizations from vulnerable to resilient.
Table of Contents
- The true cost of ignoring cybersecurity
- Evolving threats: From AI deepfakes to supply chain risks
- Cybersecurity frameworks: NIST CSF vs. ISO/IEC 27001
- Cybersecurity as a strategic business driver
- AI's dual role: Escalating attacks and empowering defense
- First steps to strengthening your organization's cybersecurity posture
- How YS Lootah Tech helps drive secure business growth
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Cyber risk impacts business value | Unchecked vulnerabilities can result in severe financial, reputational, and compliance consequences for any organization. |
| Modern threats outpace old defenses | AI-driven attacks and edge exploits require a proactive, intelligence-led posture over legacy controls. |
| Frameworks support resilient growth | Leveraging NIST or ISO frameworks structures your cybersecurity, enabling compliance and best practice integration. |
| Cybersecurity enables innovation | Integrated security turns resilience into a source of market trust and fuels transformation. |
| Continuous investment is essential | Optimal security investment and automation are necessary to keep pace with evolving risks and reduce damage. |
The true cost of ignoring cybersecurity
The financial damage from a single breach can be staggering. Beyond the immediate incident response costs, organizations face regulatory fines, litigation, and the slow erosion of customer confidence that follows any public disclosure. Cybercrime costs now equal 3% of GDP in advanced economies, a figure that puts the stakes in terms every CFO and board member can understand.
The consequences extend well beyond the balance sheet. Organizations that fail to invest in protecting business assets often discover the true cost only after an incident has already occurred. Recovery is always more expensive than prevention.
Here are the frontline consequences organizations face after a major breach:
- Lost contracts and client relationships due to damaged trust and failed security audits
- Intellectual property theft that hands competitive advantages directly to adversaries
- Regulatory penalties and fines under frameworks like GDPR, NCA, and sector-specific mandates
- Shareholder lawsuits and governance scrutiny following material disclosures
- Operational downtime that halts revenue-generating activities for days or weeks
"The question is not if your organization will face a cyber incident, but when. Leaders who treat security as a compliance checkbox will find themselves unprepared for the speed and scale of modern attacks." — Cybersecurity industry consensus, 2026
With the real financial stakes clear, it is important to understand what organizations are up against and how the threat landscape is evolving.
Evolving threats: From AI deepfakes to supply chain risks
Attackers are not standing still. The threat landscape in 2026 is defined by speed, automation, and the exploitation of trust. AI-driven phishing campaigns now generate convincing, personalized messages at industrial scale. Deepfake audio and video are being used to impersonate executives in wire transfer fraud. Supply chain attacks compromise trusted software vendors to reach hundreds of downstream targets simultaneously.
Edge and VPN exploits account for up to 20% of breaches, with a reported 34% increase in recent periods. This shift matters enormously for the impact on CIOs who are responsible for securing increasingly distributed infrastructure.
Key attack vectors your security team must address:
- Edge device and VPN exploitation targeting remote access infrastructure
- Credential compromise through phishing, credential stuffing, and MFA fatigue attacks
- Software supply chain attacks injecting malicious code into trusted third-party packages
- Living off the Land (LotL) tactics using legitimate system tools to avoid detection
| Attack type | Business impact | Recommended defense |
|---|---|---|
| AI-powered phishing | Financial fraud, data loss | Security awareness training, email filtering |
| Supply chain compromise | Widespread system access | Vendor risk management, software bill of materials |
| Edge/VPN exploits | Network intrusion | Zero-trust architecture, patch management |
| LotL persistence | Long-term undetected access | Behavioral analytics, endpoint detection |
| Deepfake social engineering | Executive fraud, reputational harm | Multi-channel verification protocols |
Pro Tip: Building a secure-by-default culture, where security is embedded in every process and product decision, consistently outperforms reactive detection strategies. Prevention is faster and cheaper than response.
Appreciating these sophisticated risks helps clarify why a compliance-only stance is no longer sufficient.
Cybersecurity frameworks: NIST CSF vs. ISO/IEC 27001
Choosing the right framework is one of the most consequential decisions a security leader makes. Two frameworks dominate enterprise conversations: NIST CSF 2.0 and ISO/IEC 27001:2022. They serve different purposes and suit different organizational contexts.
NIST CSF 2.0 defines 6 core functions: Govern, Identify, Protect, Detect, Respond, and Recover. It is outcome-based and flexible, making it ideal for organizations that want a risk management structure without pursuing formal certification. ISO/IEC 27001:2022 mandates a full Information Security Management System (ISMS) with 93 Annex A controls and requires third-party certification audits.
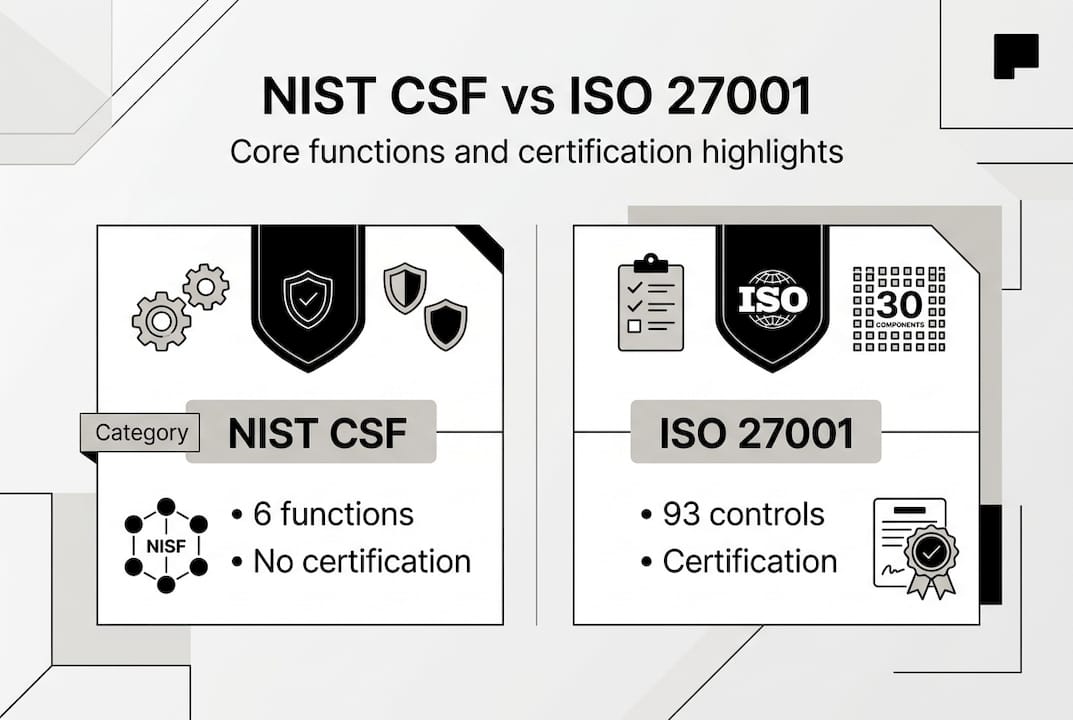
| Feature | NIST CSF 2.0 | ISO/IEC 27001:2022 |
|---|---|---|
| Certification available | No | Yes |
| Mandatory controls | No | Yes (93 Annex A controls) |
| Best for | Flexible risk management | Regulated industries, enterprise contracts |
| Audit requirement | Self-assessed | Third-party certified |
| Update cycle | Periodic guidance updates | 2022 revision, ongoing amendments |
Essential compliance steps for each framework:
- NIST CSF: Map current controls to the 6 functions, identify gaps, prioritize remediation by risk tier, and document outcomes for leadership reporting
- ISO 27001: Define ISMS scope, conduct a formal risk assessment, implement required controls, complete internal audits, and engage an accredited certification body
Pursue ISO 27001 certification when your organization operates in regulated sectors, handles sensitive customer data, or needs to demonstrate compliance to enterprise clients. NIST CSF is the right starting point when you need a structured, adaptable approach without the overhead of formal certification.
Choosing and implementing frameworks is only one part of the puzzle. Cybersecurity must be managed as a strategic enabler for enterprise growth.
Cybersecurity as a strategic business driver
The most forward-thinking organizations have stopped asking how much cybersecurity costs and started asking how much value it creates. Security is now a prerequisite for digital transformation, a differentiator in competitive bids, and a foundation for customer trust.
Business leaders must treat cybersecurity as a strategic enabler, with board integration accelerating resilience and recovery. This shift changes how budgets are allocated, how risk is communicated, and how security teams are positioned within the organization.
Robust security directly supports innovation in these ways:
- Enables faster adoption of innovative tech strategies by reducing the risk surface of new deployments
- Protects customer data, which is the foundation of digital business models
- Supports a credible digital transformation roadmap by ensuring new systems are secure from day one
- Unlocks access to regulated markets and enterprise contracts that require demonstrated security posture
- Reduces cyber insurance premiums and improves terms through documented controls
"Resilience is not a technical outcome. It is a governance outcome. Boards that integrate cybersecurity into strategic planning recover faster, lose less, and build more durable competitive advantages." — MIT Sloan Management Review, 2026
Pro Tip: Schedule a standing cybersecurity agenda item at every board meeting. When security metrics sit alongside revenue and growth data, investment decisions become faster and better aligned with actual risk.
AI's dual role: Escalating attacks and empowering defense
Artificial intelligence is reshaping both sides of the cybersecurity equation simultaneously. Attackers use AI to generate more convincing phishing content, automate vulnerability scanning, and accelerate the development of novel malware. Defenders use AI to detect anomalies faster, automate threat response, and process threat intelligence at a scale no human team can match.

Short-term, AI tactics favor attackers, but long-term, defenders who invest in data and automation gain the advantage. This asymmetry means that organizations which delay AI adoption in their security stack are falling behind, not holding steady.
AI in cybersecurity: two sides of the same edge
- Attackers use AI to: generate deepfake impersonations, automate spear-phishing at scale, discover zero-day vulnerabilities faster, and evade signature-based detection
- Defenders use AI to: detect behavioral anomalies in real time, automate incident triage, correlate threat intelligence across global data sources, and reduce mean time to respond
"The organizations that win the AI security race are those that treat automation as a force multiplier for their human analysts, not a replacement for strategic thinking." — Security Roundtable, 2026
This dynamic connects directly to how organizations manage cloud computing trends and plan for cloud infrastructure in 2026. Cloud-native environments generate enormous volumes of security telemetry that only AI-powered tools can process effectively. Stagnant security budgets in this environment do not maintain the status quo. They create wider exposure.
Grasping the people, process, and technology shifts puts business leaders in a position to take effective next steps.
First steps to strengthening your organization's cybersecurity posture
Knowing the threats and frameworks is valuable. Acting on that knowledge is what separates resilient organizations from vulnerable ones. Here are five concrete actions that deliver measurable results.
- Secure executive and board buy-in by framing cybersecurity in business risk terms, not technical jargon. Tie security metrics to revenue, reputation, and regulatory exposure.
- Conduct a formal risk assessment using NIST CSF or ISO 27001 as your baseline. Identify your most critical assets and the threats most likely to target them.
- Adopt a recognized framework and commit to continuous improvement cycles. A framework gives your team a shared language and a measurable improvement path.
- Implement defense-in-depth by layering controls across identity, endpoint, network, and data. No single control is sufficient against modern attack chains.
- Run continuous security awareness training for all staff. Human error remains the leading cause of successful breaches, and training is one of the highest-return investments available.
Optimal security spend is 2.4 times the current average, significantly reducing overall damages. When budgets are constrained, prioritize consolidating tools and automating controls before adding new point solutions.
Pro Tip: When resources are limited, consolidate your security tooling first. Fewer, better-integrated tools with automated workflows outperform a sprawling stack of disconnected point solutions every time.
For organizations starting a secure transformation, the most important step is simply starting with a clear-eyed view of current risk and a committed leadership team.
How YS Lootah Tech helps drive secure business growth
Building a resilient cybersecurity posture requires more than good intentions. It requires the right expertise, the right architecture, and a partner who understands both the technical and strategic dimensions of security.
At YS Lootah Tech, we work with business leaders and IT teams across the region to design and implement security strategies that protect operations and enable growth. Our enterprise data protection services help organizations establish robust controls aligned with leading frameworks. Our AI and security solutions bring automation and intelligence to your defense posture. And our secure application development practice ensures that every digital product you build starts with security embedded from the ground up. If you are ready to move from reactive to resilient, we are ready to help you get there.
Frequently asked questions
What are the most common cyber risks facing organizations in 2026?
AI-powered phishing, supply chain compromises, and edge/VPN exploits up 34% are the leading threats. These attack vectors are increasingly automated and difficult to detect with traditional controls.
How does NIST CSF differ from ISO/IEC 27001 for cybersecurity?
NIST CSF is a flexible, outcome-based framework with no certification requirement, while ISO 27001 mandates 93 controls and requires third-party certification audits. Regulated industries and organizations seeking to demonstrate compliance to enterprise clients typically pursue ISO 27001.
How much should my organization invest in cybersecurity?
Research shows that 2.4 times current average spend is the optimal investment level to avert $3.3 trillion in projected damages. Most organizations are significantly underinvesting relative to their actual risk exposure.
Why is cybersecurity a strategic driver, not just a compliance box?
Board integration and resilience focus consistently produce better recovery outcomes and competitive positioning than compliance-only approaches. Security enables innovation, protects customer trust, and opens access to regulated markets.