What is cybersecurity? Essential guide for business resilience

TL;DR:
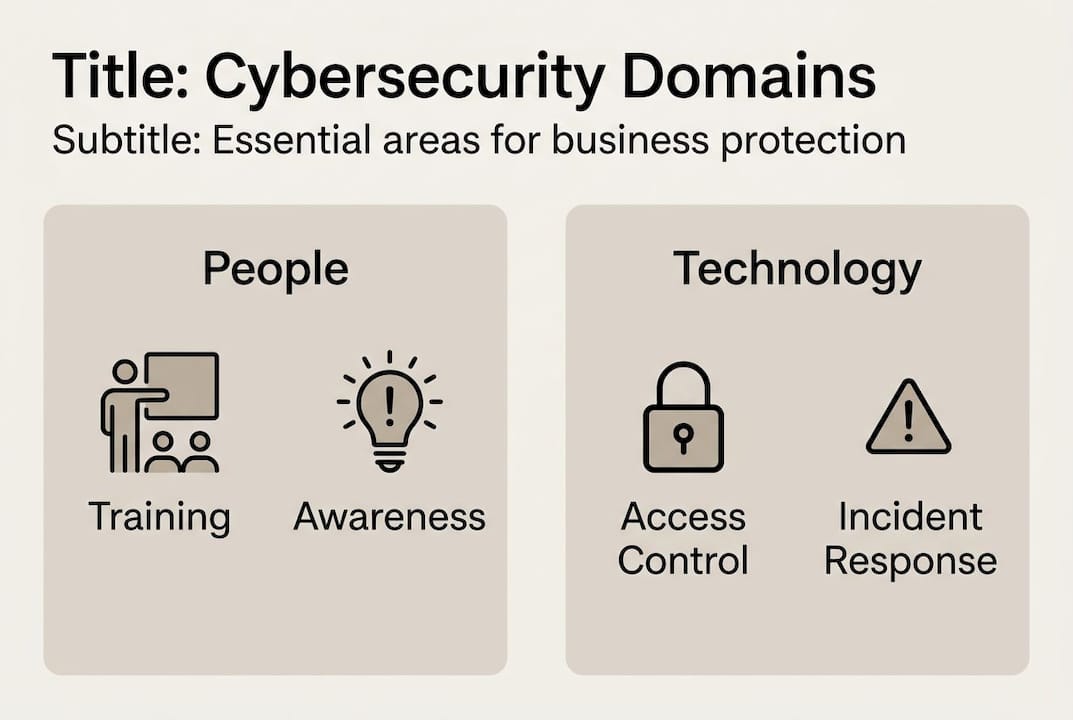
- Cybersecurity involves people, processes, and technology working together, not just firewalls.
- The NIST Cybersecurity Framework provides a structured approach with six core functions for operational resilience.
- Emerging threats like AI attacks, IoT vulnerabilities, and supply chain risks require ongoing, adaptable defenses.
The global average data breach cost hit USD 4.44 million in 2025, and nearly half of all organizations reported a cyberattack in the past year alone. Yet many business owners still picture cybersecurity as a single firewall sitting between their network and the outside world. That mental model is dangerously incomplete. Cybersecurity spans people, processes, and technology working together to protect everything your organization depends on digitally. This guide breaks down exactly what cybersecurity is, its core components, and how understanding it properly can be the difference between operational resilience and a costly, reputation-damaging breach.
Table of Contents
- Defining cybersecurity: More than just firewalls and passwords
- Key components and domains of cybersecurity
- The NIST Cybersecurity Framework and CISA Performance Goals
- Emerging threats: AI-powered attacks, IoT risks, and supply chain weaknesses
- Our perspective: Why practical cybersecurity beats perfect security
- How YS Lootah Tech can help your business stay secure
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Cybersecurity is comprehensive | It's not just technology—it includes people, processes, and policies to safeguard your business from digital threats. |
| Frameworks make security actionable | Using NIST CSF 2.0 and CISA CPGs streamlines risk management for modern organizations. |
| Emerging threats are evolving | AI-powered attacks, IoT vulnerabilities, and supply chain risks require proactive, adaptive defenses. |
| Training is critical | Educating staff on security basics averts most breaches caused by human error. |
| Perfect security is a myth | Prioritize by risk, document lessons, and aim for resilience, not unattainable perfection. |
Defining cybersecurity: More than just firewalls and passwords
Cybersecurity is one of those terms that gets used constantly but rarely defined with precision. Most people assume it means antivirus software and strong passwords. In reality, it goes far deeper than that.
"Cybersecurity is the practice of protecting systems, networks, and data from digital threats using strategies, tools, and frameworks." — NIST NICE Framework
Notice what that definition does not say. It does not say "install a firewall and call it a day." It references strategies, tools, and frameworks, meaning cybersecurity is a discipline that requires deliberate planning, ongoing management, and organizational commitment.
For IT managers and business leaders, this distinction matters enormously. A firewall stops certain traffic at the perimeter. But what happens when a phishing email gets through and an employee clicks a malicious link? What happens when a contractor with access to your systems gets compromised? Technology alone cannot answer those questions. People and process must.
Some of the most persistent myths about cybersecurity keep businesses dangerously exposed:
- "Our business is too small to be a target." Attackers often prefer small businesses precisely because defenses tend to be weaker.
- "We have antivirus software, so we're protected." Antivirus catches known threats. Modern attacks frequently use novel techniques that signature-based tools miss.
- "Cybersecurity is purely an IT problem." Breaches often originate from HR, finance, or executive-level accounts. Everyone is part of the security posture.
- "We've never been attacked, so our defenses must work." Many breaches go undetected for months. Absence of evidence is not evidence of absence.
- "Compliance equals security." Meeting a regulatory standard is a floor, not a ceiling. Compliance frameworks are a starting point, not a complete defense.
Understanding enterprise cybersecurity fundamentals means accepting that cybersecurity is a living, breathing organizational function, not a one-time technology purchase. It requires leadership buy-in, clear policies, trained staff, and technology that works together in a coordinated way.

Key components and domains of cybersecurity
With a foundational definition established, let's explore what actually makes up effective organizational cybersecurity. The discipline is not monolithic. It breaks into distinct domains, each addressing a different attack surface or risk category.
According to the NIST NICE Framework, key cybersecurity sectors include end-user education, physical security, critical infrastructure security, cloud security, incident recovery, and network security. Here is how those domains translate into practice:
| Domain | Focus area | Example practice |
|---|---|---|
| End-user education | Human behavior and awareness | Phishing simulation training |
| Network security | Traffic monitoring and control | Firewalls, intrusion detection |
| Cloud security | Data and apps in cloud environments | Identity access management |
| Critical infrastructure | Operational technology protection | Segmented industrial networks |
| Incident recovery | Restoring operations after breach | Tested backup and recovery plans |
| Physical security | Preventing physical access threats | Badge access, camera systems |
Two domains that organizations frequently underestimate are insider threats and third-party risks. An employee with excessive access permissions, whether acting maliciously or carelessly, can cause as much damage as an external attacker. Similarly, vendors and contractors who connect to your systems extend your attack surface in ways that are easy to overlook.
The assets worth protecting go beyond servers and laptops:
- Customer personally identifiable information (PII)
- Intellectual property and trade secrets
- Financial records and payment data
- Operational systems and production environments
- Employee credentials and HR data
Understanding the importance of data security across all these asset categories is what separates organizations that recover quickly from those that don't recover at all. Effective security awareness strategies should be tailored to your industry, your team size, and the specific data you handle.
Pro Tip: Prioritize user training before investing in more technology. Studies consistently show that human error is the leading cause of breaches, making your people both the biggest vulnerability and your strongest potential defense.
The NIST Cybersecurity Framework and CISA Performance Goals
To organize cybersecurity efforts strategically, frameworks provide actionable paths for business resilience. Two of the most widely respected are the NIST Cybersecurity Framework (CSF) 2.0 and the CISA Cross-Sector Cybersecurity Performance Goals.
The NIST CSF 2.0 structures cybersecurity around six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. Think of these as a continuous cycle rather than a linear checklist.
| CSF 2.0 function | What it means for your business |
|---|---|
| Govern | Set policies, roles, and risk tolerance at leadership level |
| Identify | Know what assets and risks exist in your environment |
| Protect | Put controls in place to limit or contain impact |
| Detect | Monitor systems to find threats quickly |
| Respond | Execute a plan when an incident occurs |
| Recover | Restore operations and learn from the event |
The CISA CPG Report 2.0 translates this into prioritized IT and OT (operational technology) practices that any organization can act on immediately, regardless of size or sector. These goals cover areas like asset inventory, access management, and vulnerability patching.
Here is a practical sequence for aligning your operations with these frameworks:
- Conduct a full inventory of digital assets, including shadow IT and third-party connections.
- Define your organization's risk tolerance and document it formally.
- Implement multi-factor authentication (MFA) across all critical systems.
- Establish a vulnerability management program with defined patching timelines.
- Build and test an incident response plan before you need it.
- Review and update controls at least annually or after any significant change.
Working with experts who can reduce cyber risk with support makes this alignment faster and more accurate, especially for organizations without a dedicated security team.
Pro Tip: Start with the "Govern" function. Without clear ownership, defined risk appetite, and leadership accountability, every other security investment becomes harder to sustain and measure.
Emerging threats: AI-powered attacks, IoT risks, and supply chain weaknesses
While frameworks give structure, the threat landscape keeps evolving. Here is what you need to know about today's most dangerous risks.
AI-powered attacks are no longer theoretical. Attackers now use large language models to craft convincing phishing emails at scale, automate vulnerability scanning, and even generate malware that adapts to evade detection. "Agentic AI" refers to AI systems that can take autonomous actions, and threat actors are beginning to deploy these capabilities offensively. The speed advantage this gives attackers is significant.
As noted by cybersecurity researchers, legacy and unpatchable IoT software remains a critical vulnerability, AI-driven threats are accelerating attack timelines, and supply chain and third-party risks continue to amplify breach impact across industries.
The emerging threats your organization needs to account for include:
- Legacy IoT devices that cannot be patched and sit quietly on your network as entry points
- AI-generated phishing that is nearly indistinguishable from legitimate communications
- Supply chain attacks where a trusted vendor becomes the vector for a breach
- Ransomware-as-a-service platforms that lower the technical barrier for attackers
- AI misalignment risks in automated systems that make security decisions without full context
The numbers reinforce the urgency. The 2025 breach cost report shows 44% of breaches involved ransomware, and 70% of organizations remained in low readiness stages despite known risks. Third parties were involved in nearly 30% of all breaches, making vendor risk management a non-negotiable priority.
Understanding strategic protection in 2026 means accounting for these vectors now, not after an incident. Staying current on 2026 cybersecurity trends and applying innovative cyber strategies gives your organization a meaningful head start against threats that are becoming faster and more sophisticated every quarter.
Our perspective: Why practical cybersecurity beats perfect security
Here is the uncomfortable truth that most cybersecurity vendors will not tell you: perfect security does not exist. Every system has a flaw. Every process has a gap. Every human makes mistakes. Chasing an impossible standard of zero risk leads organizations to either overspend on tools they cannot operate effectively or freeze entirely, doing nothing while the threats pile up.
What actually works is a risk-based approach. Identify what matters most to your business, understand the realistic threats against it, and invest proportionally. Most breaches we see in practice do not come from sophisticated nation-state attacks. They come from unpatched software, reused passwords, and employees who were never trained to recognize a phishing attempt.
Investing in people and process often delivers more security per dollar than the next technology purchase. Security is an ongoing journey, not a destination. The organizations that handle incidents best are the ones that have documented lessons from previous events and built those lessons into their next cycle of improvement. Reviewing best practices for enterprise security regularly keeps that cycle moving.
Pro Tip: After any security incident, document what happened, what worked, and what failed. That debrief is worth more than most security audits.
How YS Lootah Tech can help your business stay secure
Equipped with a realistic outlook, here is how our expertise becomes your advantage.
At YS Lootah Tech, we build security into every layer of the digital solutions we deliver, not as an afterthought but as a design principle. Our secure application development and secure website development services are built around modern security standards from the ground up. We also integrate AI-driven cybersecurity capabilities that help detect anomalies, automate threat response, and reduce the window between attack and containment. Whether you are starting a digital transformation or hardening an existing infrastructure, our team provides the strategic guidance and technical execution your organization needs to stay resilient.
Frequently asked questions
What is the simplest explanation of cybersecurity?
Cybersecurity is the practice of protecting your data, systems, and network from digital threats using strategies, technology, and policies. It covers everything from how your team handles passwords to how your organization responds when something goes wrong.
Why is cybersecurity crucial for small businesses too?
Small businesses are frequent targets because their defenses tend to be weaker, and a single incident can cause serious financial and reputational damage. With 49% of organizations reporting a cyberattack in the past year, no business is too small to be on an attacker's radar.
What are the top three actions to improve business cybersecurity?
Inventory your digital assets, train all staff on security basics, and implement access and vulnerability management controls. The CISA CPGs identify these as foundational priorities that deliver the highest return on security investment.
How do AI and automation help reduce cyberattack costs?
AI and automation detect and contain threats faster than manual processes, cutting breach costs by up to USD 1.9 million for businesses that deploy them effectively. AI-powered containment reduced global breach costs by 9% in 2025 alone.
What is the NIST Cybersecurity Framework?
The NIST Cybersecurity Framework is a structured guide that helps organizations manage security through six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. It is designed to be adaptable for organizations of any size or industry.