Enterprise security explained: frameworks, risks, and steps

TL;DR:
- Enterprise security requires a continuous, integrated approach involving people, processes, and technology.
- Frameworks like NIST CSF 2.0 emphasize leadership involvement and proactive risk management.
- Accepting "good enough" security and building resilience often outperform chasing perfect protection.
The average data breach now costs U.S. enterprises over $9 million per incident, yet many leadership teams still treat cybersecurity as an IT purchasing problem. Buy the right firewall, deploy the right software, and you're protected. That assumption is exactly what attackers count on. Enterprise security is a discipline that spans people, processes, and technology together, and when any one of those layers is weak, the whole posture collapses. This article breaks down what enterprise security actually means, which frameworks should guide your strategy in 2026, and what concrete steps you can take to build a resilient, defensible organization.
Table of Contents
- What is enterprise security?
- Essential components of enterprise security
- Frameworks that guide modern enterprise security
- New realities: Risk quantification, AI, and security culture
- The uncomfortable truth: Perfect security doesn't exist—and why 'good enough' wins
- Your next move: Building secure, resilient digital operations
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Enterprise security is holistic | It integrates people, processes, and technology with a strong leadership focus. |
| Frameworks set the standard | NIST CSF 2.0 and CISA CPG 2.0 offer clear guidance for structured security programs. |
| Financial risk and AI matter | Advanced trends like risk quantification and AI are reshaping both threats and defenses. |
| Perfect is impossible | Aim for resilient, business-aligned 'good enough' security over unattainable perfection. |
What is enterprise security?
Enterprise security is the coordinated practice of protecting an organization's data, systems, people, and operations from threats that range from technical exploits to human error. It is not a product you buy. It is a continuous program you build, maintain, and evolve.
The financial stakes make this distinction urgent. The average data breach cost reached $4.45 million globally in 2025, with U.S. enterprises absorbing more than double that figure. Vulnerability exploitation caused 40% of incidents, and ransomware groups grew 49% year over year according to IBM's 2026 X-Force Threat Index. Those numbers are not abstract. They represent operational shutdowns, regulatory fines, reputational damage, and lost customer trust.
"Security is only as strong as its weakest link, and in most enterprises, that link is not a misconfigured server. It is a process no one documented, a policy no one enforced, or a person no one trained."
The misconception that security equals technology leads organizations to invest heavily in tools while neglecting governance and culture. A next-generation endpoint solution cannot compensate for employees who click phishing links because they never learned to recognize them. Encryption is useless if access controls are poorly managed. Technology amplifies good practices. It cannot replace them.
Threats facing enterprises today fall into three broad categories:
- Technical exploits: Vulnerabilities in software, misconfigurations, and unpatched systems that attackers actively scan for and weaponize.
- Social engineering: Phishing, spear-phishing, and business email compromise that manipulate people rather than systems.
- Human error: Accidental data exposure, misconfigured cloud storage, and insider mistakes that account for a significant share of breaches.
Understanding this landscape is the first step. Reviewing enterprise security best practices gives you a sharper picture of how each threat type maps to specific controls.
Essential components of enterprise security
With the big-picture definition in place, let's break down the moving parts of a complete enterprise security strategy. A mature program integrates several interdependent components, and skipping even one creates exploitable gaps.
Key components of a complete enterprise security strategy include identity and access management, network security, endpoint detection and response, data encryption, vulnerability management, incident response planning, and security awareness training. Each one is load-bearing.
- Identity and access management (IAM): Controls who can access what, and under what conditions. Enforcing least-privilege access and multi-factor authentication here prevents a huge share of breaches before they start.
- Network security: Firewalls, segmentation, and intrusion detection systems that limit lateral movement once an attacker is inside your perimeter.
- Endpoint detection and response (EDR): Continuous monitoring of devices to detect and contain threats in real time, not just block known malware signatures.
- Data encryption: Protecting data at rest and in transit so that stolen information remains unreadable without the correct keys.
- Vulnerability management: Continuous scanning, prioritization, and patching of weaknesses before attackers find them. This is where the 40% exploitation statistic hits hardest.
- Incident response planning: Documented playbooks, assigned roles, and regular drills so your team acts decisively when something goes wrong, not reactively.
- Security awareness training: The human layer. Regular, scenario-based training that builds instinct, not just compliance checkboxes.
The role of core security measures is not to eliminate risk entirely. It is to make your organization a harder, more expensive target than the next one. Attackers optimize for ease. Make ease unavailable.

Pro Tip: Don't treat incident response planning as a one-time document. Run tabletop exercises quarterly with both IT and executive stakeholders. The enterprise applications role in incident response is often underestimated until a critical system goes offline mid-breach.
Frameworks that guide modern enterprise security
The foundation is components, but the playbook is set by frameworks. Here's how leading standards guide real enterprise security decisions in 2026.
The NIST Cybersecurity Framework 2.0 structures enterprise security around six functions that form a complete operational cycle. The newest addition, "Govern," signals a deliberate shift: security is now explicitly a leadership responsibility, not just an IT function.
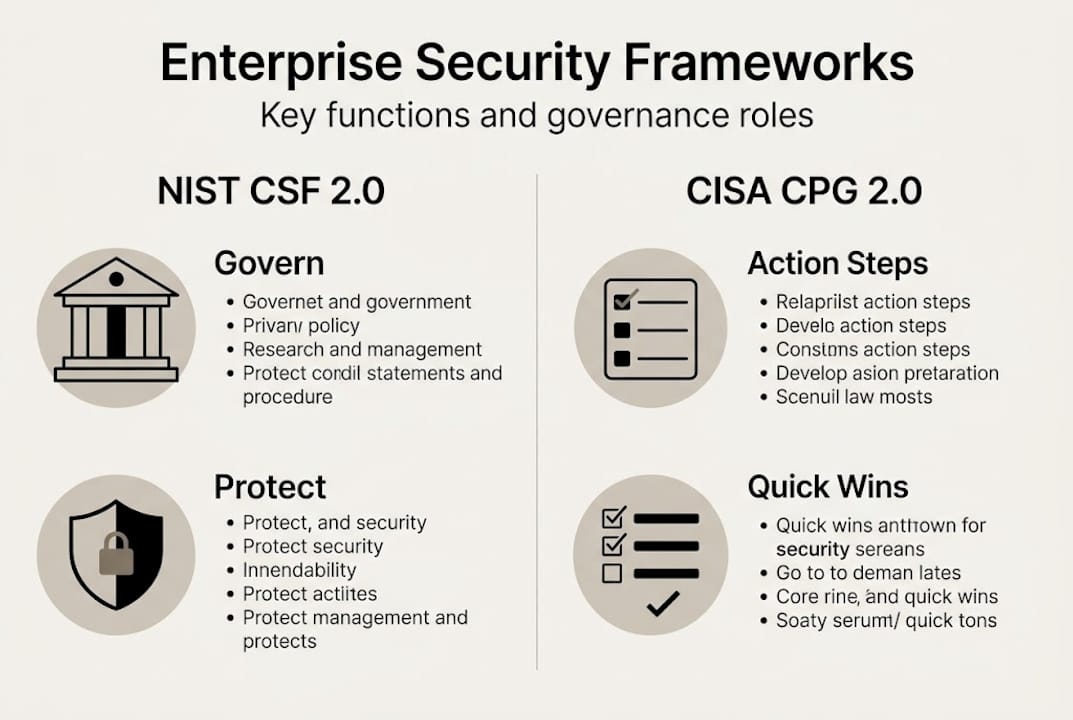
| NIST CSF 2.0 function | Core purpose | CISA CPG 2.0 alignment |
|---|---|---|
| Govern | Leadership oversight, risk strategy, policy | New in CPG 2.0; drives accountability |
| Identify | Asset inventory, risk assessment | Foundational baseline controls |
| Protect | Access controls, data security, training | Prioritized protective measures |
| Detect | Continuous monitoring, anomaly detection | Detection performance goals |
| Respond | Incident response, communications | Response playbook requirements |
| Recover | Recovery planning, improvements | Resilience and continuity goals |
CISA CPG 2.0 translates this framework into prioritized, actionable IT and OT practices for critical infrastructure operators. Where NIST CSF 2.0 is strategic, CPG 2.0 is operational. Together, they give you both the map and the directions.
The governance shift in NIST is the most important development for executives to internalize. "Govern" means your board and C-suite are now expected to own cybersecurity risk the same way they own financial or operational risk. Security decisions must connect to business outcomes, not just technical metrics. This is where most organizations still lag.
Understanding the NIST Cybersecurity Framework explained in plain business terms helps leadership teams engage meaningfully with their security teams rather than simply signing off on budgets.
New realities: Risk quantification, AI, and security culture
With the frameworks and basics established, the newest challenges and most promising defenses are reshaping what next-level enterprise security means in practice.
Financial risk quantification is changing how security investments get approved. Cyber Risk Quantification (CRQ) using the FAIR model translates threat scenarios into dollar-denominated estimates. Instead of telling the CFO "we need better endpoint protection," you say "a ransomware event in our logistics system carries a $3.2 million expected annual loss." That language moves budgets. Outcome-driven governance paired with continuous CRQ/FAIR benchmarking is how high-performing security teams earn executive trust and funding.
AI is a double-edged reality. Attackers use it to generate convincing phishing content at scale, automate vulnerability scanning, and craft adaptive malware. Defenders use it to detect anomalies faster, correlate threat intelligence, and reduce analyst fatigue. The organizations winning this arms race invest in AI-driven cyber defense while training their teams to recognize AI-generated social engineering.
Here is a practical framework for leveling up across all three areas:
- Quantify your top five risks using FAIR methodology and present findings to leadership in financial terms.
- Audit your AI exposure by mapping which systems use AI and which threat vectors target them specifically.
- Redesign security training around scenario simulations, not annual slide decks. Frequency and realism matter more than duration.
- Establish a security culture metric by tracking phishing simulation click rates and near-miss reporting over time.
- Review your security culture trends quarterly and adjust your awareness program based on what is actually failing.
Pro Tip: Organizations that lag in adoption due to resource constraints should start with CISA CPGs as a simplified baseline rather than trying to implement the full NIST CSF at once. Prioritization beats paralysis.
| Area | Common gap | Quick win |
|---|---|---|
| Risk quantification | No financial framing | Run one FAIR scenario per quarter |
| AI defense | Reactive posture | Enable AI-assisted anomaly detection |
| Security culture | Annual training only | Monthly phishing simulations |
The uncomfortable truth: Perfect security doesn't exist—and why 'good enough' wins
Here is something most security vendors will never tell you: no organization achieves perfect security. The ones that perform best are not the ones chasing zero risk. They are the ones who accept that breaches will happen, build for rapid detection and recovery, and treat every incident as a learning opportunity rather than a failure to hide.
Chasing perfect security leads to security theater. You end up with impressive dashboards, long compliance reports, and a false sense of protection. Real resilience comes from honest risk prioritization, business-aligned controls, and a culture that rewards transparency over blame.
High-performing enterprises make deliberate trade-offs. They protect their crown jewels aggressively and accept higher risk tolerance in lower-value systems. They invest in innovation through pragmatic risk management rather than trying to lock down everything equally. That flexibility is not weakness. It is strategic maturity. A "good enough" security posture that your team actually executes consistently will always outperform a theoretically perfect program that collapses under operational pressure.
Your next move: Building secure, resilient digital operations
Knowing the frameworks and components is only half the work. The other half is building systems and applications that are secure by design from the start.
At YS Lootah Tech, we help enterprises in Dubai and across the region embed security into every layer of their digital operations. From secure application development that integrates security controls at the code level, to enterprise website solutions built with resilience in mind, our teams work alongside your IT and executive stakeholders to align technology with your risk posture. If you are ready to move from reactive patching to proactive protection, our digital transformation services give you a structured path forward.
Frequently asked questions
How do NIST CSF 2.0 and CISA CPG 2.0 differ for enterprise security?
NIST CSF 2.0 is a broad strategic framework, while CISA CPG 2.0 provides prioritized, practical security goals aligned with NIST specifically for critical infrastructure operators. Think of NIST as the strategy and CPG as the execution checklist.
What is the role of 'Govern' in the latest security frameworks?
The "Govern" function places cybersecurity risk ownership at the leadership level, requiring executives and boards to integrate security decisions into overall enterprise risk management rather than delegating them entirely to IT.
Why is financial risk quantification significant for security decisions?
Financial risk quantification translates technical threats into business-language dollar estimates, helping security leaders make a compelling case for investment and helping executives prioritize resources based on actual potential impact.
How does AI affect enterprise security today?
AI accelerates both attacks and defenses simultaneously. Attackers use it to automate and personalize threats at scale, while defenders use it to detect anomalies and reduce response times significantly.
Can smaller organizations implement these enterprise-level security strategies?
Yes. Organizations with limited resources should start with simplified baselines like CPGs and implement the most critical controls first, scaling up as capacity grows rather than attempting full framework adoption immediately.