Data security guide: 7 steps for Middle East businesses

TL;DR:
- A single data breach in the Middle East costs an average of SAR 27 million.
- Effective cybersecurity requires risk assessment, foundational controls, and advanced data protection.
- Zero Trust architecture and AI-enhanced security are essential for modern threat mitigation.
A single data breach in the Middle East now costs an average of SAR 27 million, even after an 18% drop driven by AI, encryption, and DevSecOps adoption. That number represents lost revenue, regulatory fines, customer trust, and operational downtime, all at once. For business owners and IT managers across the Gulf, this is not a distant risk. It is a present threat that requires a structured, practical response. This guide walks you through the steps to assess your exposure, build strong defenses, and stay ahead of the threats that are actively targeting organizations in this region.
Table of Contents
- Assess your current risk landscape
- Set up foundational security controls
- Deploy advanced data-centric protection
- Protect against emerging threats and AI-driven risks
- Our perspective: What Middle East organizations get wrong about data security
- Strengthen your data security with expert help
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Understand your risk landscape | Identifying your organization's key vulnerabilities is the foundation of effective data security. |
| Build on solid basics | Establish access control, strong authentication, and encryption as essential defenses. |
| Adopt Zero Trust for advanced security | Continuous verification and a data-centric model provide stronger protection for modern environments. |
| Stay ahead of emerging threats | Anticipate AI-driven and non-human identity risks by routinely updating your security strategy. |
| Invest in ongoing improvement | Regular assessment and adaptation keep your organization resilient as technology and threats evolve. |
Assess your current risk landscape
Before you can fix a security problem, you need to understand exactly where you are exposed. Many organizations skip this step and jump straight to buying tools. That approach wastes budget and leaves real gaps open.
The Middle East threat environment is specific. Top attack vectors in the region include third-party and supply chain breaches at 17%, followed by phishing and denial-of-service attacks at 14% each. Understanding supply chain attacks is especially important because these often bypass your internal defenses entirely by targeting a vendor or partner you already trust.
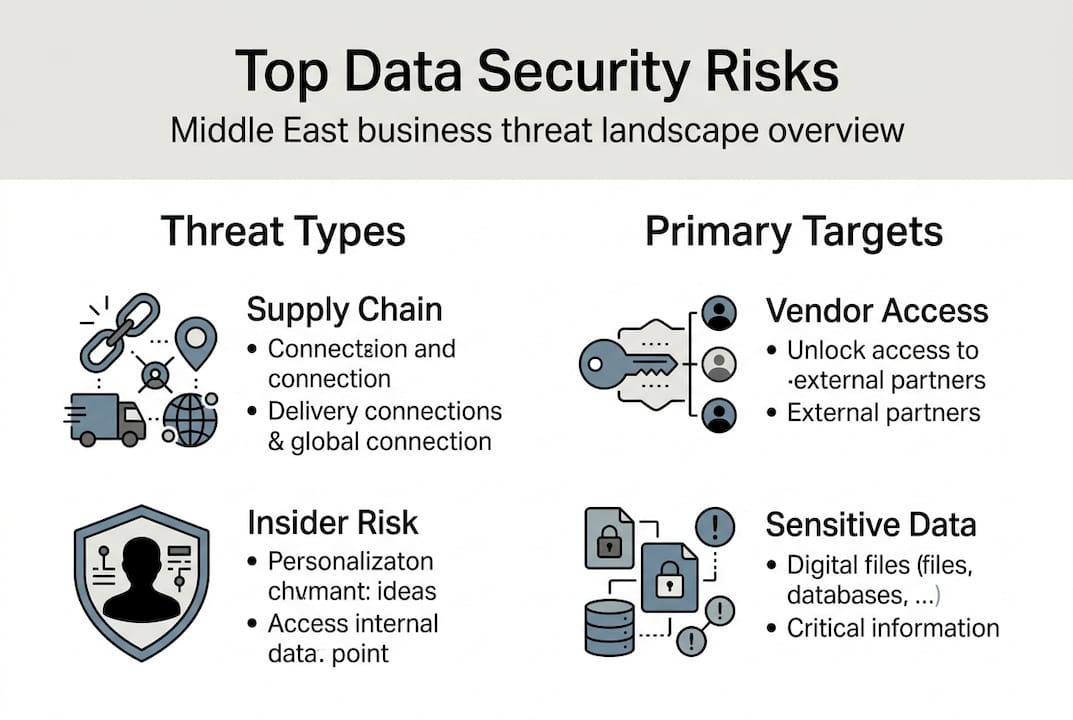
Here is a breakdown of the most common threat categories and what they target:
| Threat type | Frequency in region | Primary target |
|---|---|---|
| Third-party/supply chain | 17% | Vendor access, shared systems |
| Phishing | 14% | Employee credentials, email |
| Denial-of-service | 14% | Availability, operations |
| AI model attacks | Growing | Training data, model outputs |
| APT group intrusions | 32% of attacks | Government, finance, energy |
Advanced persistent threat (APT) groups, which are organized, state-linked attackers who operate quietly over long periods, account for 32% of attacks in the region. The UAE and Saudi Arabia are among the most targeted countries on the dark web. This is not generic cybercrime. It is coordinated, patient, and often sector-specific.
When assessing your risk, focus on these key areas:
- Critical data assets: customer records, financial data, intellectual property, and operational systems
- Employee access points: who has access to what, and whether that access is still needed
- Third-party connections: every vendor, SaaS tool, and API integration is a potential entry point
- Digital infrastructure: unpatched software, legacy systems, and misconfigured cloud environments
Understanding data security importance at this foundational level is what separates organizations that react to breaches from those that prevent them.
Pro Tip: Use a simple risk matrix. List your top 10 data assets, rate the likelihood and impact of each being compromised, and prioritize your security investments accordingly.
Set up foundational security controls
Once you know your risks, reinforce your foundation with essential security controls. These are not glamorous, but they are the measures that consistently prevent the majority of breaches.

Access control is your first line of defense. Apply the principle of least privilege, meaning every user and system should only have access to what they absolutely need. Combine this with multi-factor authentication (MFA) across all critical systems. MFA alone blocks the vast majority of credential-based attacks.
Encryption is equally non-negotiable. Encrypt data both at rest (stored on servers or devices) and in transit (moving across networks). Encryption and DevSecOps practices were directly linked to an 18% drop in breach costs across the Middle East, which is a clear signal that these controls deliver measurable financial protection.
Your foundational security checklist should include:
- MFA on all accounts: email, cloud platforms, VPNs, and admin portals
- Role-based access control (RBAC): define access by job function, not by individual request
- End-to-end encryption: for all sensitive data, both stored and transmitted
- Automated backups: daily backups stored in a separate, isolated environment
- Backup restoration tests: run a full restoration drill at least quarterly
- Basic incident response plan: a written, practiced plan for what to do in the first 24 hours of a breach
Do not underestimate the backup step. Many organizations discover their backups are corrupted or incomplete only when they actually need them. Cutting breach risk starts with ensuring your recovery options actually work.
Pro Tip: Treat your incident response plan like a fire drill. Run a tabletop exercise with your IT team and key business leaders at least twice a year. The goal is to make the first hour of a breach feel familiar, not chaotic.
Deploy advanced data-centric protection
With your foundation in place, consider advanced methods to protect your data at its core. Traditional perimeter security, which means firewalls and VPNs guarding the edge of your network, was designed for a world where all your data lived inside your office. That world no longer exists.
Cloud, hybrid, and SaaS environments mean your data moves constantly across systems, vendors, and geographies. Perimeter security fails in these environments because there is no longer a clear boundary to defend. Zero Trust architecture addresses this by eliminating implicit trust entirely.
Here is how the three main models compare:
| Security model | Core assumption | Best suited for |
|---|---|---|
| Traditional perimeter | Trust inside the network | On-premise, static environments |
| Zero Trust | Never trust, always verify | Cloud, hybrid, remote workforces |
| Data-centric | Protect the data itself | Multi-cloud, SaaS-heavy operations |
Zero Trust requires continuous verification of every user, device, and data flow, regardless of location. It also uses micro-segmentation, which means dividing your network into small zones so that a breach in one area cannot spread freely.
Zero Trust data security secures the data itself rather than the perimeter around it. This shift is fundamental, not cosmetic.
To implement Zero Trust in practice, follow this sequence:
- Verify identities: implement strong identity management with MFA and single sign-on (SSO)
- Secure devices: enforce device health checks before granting any access
- Map data flows: understand exactly where your sensitive data travels and who touches it
- Apply micro-segmentation: isolate critical systems so lateral movement is blocked
- Monitor continuously: log all access and use behavioral analytics to flag anomalies
For organizations exploring cloud security trends, Zero Trust is no longer optional. It is the architecture that makes cloud adoption safe. Learn more about building a business data protection framework that fits your specific environment.
Protect against emerging threats and AI-driven risks
New technologies bring both innovation and risks. Make sure your data security evolves as quickly as your tech stack.
The threat landscape in 2026 includes attack vectors that did not exist three years ago. Non-human identities, SaaS data movement, and AI agents create entirely new categories of risk. A service account with excessive permissions, an AI agent with write access to your database, or synthetic training data that has been poisoned are all real, active concerns.
Statistic to know: Tight access controls on AI models mitigated 41% of AI-related attacks in the Middle East. That is a significant return on a relatively straightforward security measure.
Use this checklist when adopting any new AI or SaaS tool:
- Audit non-human identities: catalog every service account, API key, and bot with system access
- Apply least privilege to AI agents: AI tools should only access the data they need for their specific function
- Monitor data movement in SaaS: track what data leaves your environment and where it goes
- Validate synthetic data sources: if you use synthetic data for training or testing, verify its integrity and origin
- Review third-party AI integrations: every AI vendor you connect to is a potential supply chain risk
- Use AI defensively: deploy AI and ML capabilities for anomaly detection, automated threat response, and log analysis
AI is a double-edged tool. Attackers use it to craft more convincing phishing emails, automate vulnerability scanning, and evade detection. Defenders use it to process threat intelligence faster than any human team could. Staying current on latest cloud risks means understanding both sides of that equation.
Pro Tip: Before deploying any AI-powered tool in your organization, run a short security review. Ask the vendor three questions: where does my data go, who can access it, and how is it protected at rest and in transit?
Our perspective: What Middle East organizations get wrong about data security
After working closely with enterprises across the Gulf, we have noticed a persistent pattern. Most organizations invest heavily in perimeter defenses, firewalls, VPNs, and network monitoring, and then assume they are protected. They are not.
Attackers in this region are sophisticated. APT groups do not knock on the front door. They enter through a trusted vendor, a compromised employee account, or an overlooked API. By the time a perimeter alert fires, the attacker has often been inside for weeks.
The real shift comes when organizations stop asking "how do we keep attackers out?" and start asking "what happens if they are already in?" That question leads to Zero Trust, micro-segmentation, and data-centric protection. It leads to comprehensive data protection strategies that assume breach and minimize damage.
We also see a collaboration gap. IT teams build security controls in isolation, without input from business leaders or compliance teams. That creates policies nobody follows and gaps nobody notices. True security transformation in the Middle East requires all three groups working from the same playbook.
Strengthen your data security with expert help
The steps in this guide are actionable, but implementing them across a live business environment requires the right expertise and tools. That is where we come in.
At YS Lootah Tech, we help Middle East enterprises build security frameworks that match their real risk profile, not a generic template. From enterprise data protection strategies to secure application development and AI and ML-based security tools, our team brings hands-on regional experience to every engagement. Whether you are starting from scratch or strengthening an existing program, we can help you move faster and smarter. Reach out to schedule a tailored security consultation and take the first concrete step toward protecting what matters most.
Frequently asked questions
What is the most effective first step to improve data security in my business?
Start by mapping your most critical data assets and identifying your highest-risk access points. Top attack vectors in the Middle East include supply chain, phishing, and denial-of-service, so your risk assessment should address all three.
How does Zero Trust differ from traditional security measures?
Traditional security trusts anything inside the network perimeter. Zero Trust requires continuous verification of every user and device, and protects the data itself rather than the boundary around it.
How can AI and machine learning help reduce data breach costs?
AI and ML accelerate threat detection and automate response, which directly reduces the time a breach goes undetected. These tools contributed to an 18% drop in breach costs across the Middle East in 2025.
What emerging risks should I be aware of when adopting AI or SaaS solutions?
Non-human identities, AI agents, and SaaS data movement introduce risks that traditional security tools were not designed to handle. Audit every new integration before it goes live.
Why do Middle East companies face unique cybersecurity challenges?
The region is actively targeted by APT groups that account for 32% of attacks, with the UAE and Saudi Arabia among the most exposed countries. Sector-specific targeting in finance, energy, and government adds further complexity.